Edition 1.3 Googled Security Events Corner
Google News Search
Sorted by relevance
Sort by date Sort by date with duplicates included
LIGATT Security International Signs Letter of Intent to Purchase …
MarketWatch – 20 hours ago
This purchase will help assist LIGATT Security in the distribution of computer security and cyber crime products and services. …
Cyber security minister ridiculed over s’kiddie hire plan
Register – John Leyden – 22 hours ago
Security experts have strongly criticised suggestions by a government minister that former hackers might play a …
Cybercrime spreads on Facebook
Reuters – Jim Finkle – 15 hours ago
Always,” said Mary Landesman, a senior researcher at Web security company ScanSafe. Scammers break into accounts posing as friends of users, sending spam …
Military Command Is Created for Cyber Security
Wall Street Journal – Siobhan Gorman, Yochi Dreazen – Jun 23, 2009
Maren Leed, a cyber-security expert at the Center for Strategic and International Studies, said the military’s closed computer networks could make it easier …
Gates Creates Cyber-Defense Command Washington Post
New Military Command for Cyberspace New York Times
Ex-DHS Cyber Chief Tapped as President of ICANN
Washington Post – Brian Krebs – Jun 26, 2009
Most recently, Beckstrom was director of the National Cyber Security Center — an organization created to coordinate security efforts across the …
Ex-DHS Cyber Exec to Head ICANN GovInfoSecurity.com
Icann appoints new head honcho V3.co.uk
US Cyber Command: 404 Error, Mission Not (Yet) Found
Wired News – Noah Shachtman – Jun 26, 2009
(Another: what does a recent and classified National Intelligence Estimate on cyber security recommend.) But already, there’s tough talk in and around the …
Video: Britain launches cyber-terror strategy![]()
ITN NEWS
Britain says facing growing cyber security threat Reuters
UK Employs ‘Naughty Boys’ to Battle Other Hackers Wired News
Delegate Question Cyber Attack Investigation
NBC 29 News – Adam Rhew – 13 hours ago
“Do we have ongoing processes to secure the system and maintain a level of security,” Del. Kathy Byron (R-22nd District) asked. …
Some prescriptions halted in Va. due to hacker The Associated Press
Former DHS Cybersecurity Head Lands at ICANN
Wired News – Kim Zetter – 16 hours ago
It’s hoped that Beckstrom will help smooth out some of the organization’s ripples and aid its efforts to address security concerns such as domain name …
Former DHS IT official to head ICANN FierceGovernmentIT
ICANN Hires Former Cybersecurity Chief As New CEO Sci-Tech Today
Obama and Cyber Defense
Wall Street Journal – Jun 28, 2009
It’s an open secret that the National Security Agency (NSA) must operate through civilian networks inside the US in order to prevent millions of cyber …
Common defense absent from cybersecurity Defense Systems
NATO hawks are circling as the Web readies for tighter surveillance Taipei Times
Balancing Computer Security and Innovation—A Talk with RSA’s Art …
Xconomy – Wade Roush – Jun 29, 2009
A preview: he’s reserved, but optimistic—and has some specific suggestions on who President Obama should name as the new cyber security czar. …
Google Blog Search
iKeepSafe Coalition: Promoting Cyber Safety, Security, and Ethics …
12 hours ago by Internet Keep Safe Coalition
Of the teens who admit to cheating with their cell phones, 26 percent say they store information on their phone to look at during a test, 25 percent text friends about answers during a test, 17 percent take pictures of the test to send …
iKeepSafe Coalition: Promoting Cyber Safety,… – http://ikeepsafe.blogspot.com/ – References
[ More results from iKeepSafe Coalition: Promoting Cyber Safety,… ]
First Cyber Security Measures Unveiled | TTKN News
27 Jun 2009 by admin
The Prime Minister said the UK’s first national Cyber Security Strategy paves the way for extra funding and new measures to help detect cyber attacks. The. … Mr Brown said the internet and the flow of information has risen dramatically around the world, which has in turn increased the risk. ?Some terrorist groups are using the internet in a wholly exploitative way and of course we have got to beware of any threats to our country.? The PM added: …
TTKN News – http://www.ttkn.com/ – References
Rise in Cyber Crime, Cyber Terrorism and Cyber Espionage Tied …
14 hours ago by admin
Cyber crime has gained significant international mobility. In 2007, Estonian computer networks were crippled when serious distributed denial of service (DDoS) attacks against government and civilian sites were reputedly linked back to … Trend Micro Incorporated, a global leader in Internet content security, focuses on securing the exchange of digital information for businesses and consumers. A pioneer and industry vanguard, Trend Micro is advancing integrated threat …
The Tech Release – http://www.thetechrelease.com/
City firm to help ensure nation’s data security
23 hours ago by The Desk
The idea behind the DSCI is to have a credible body to maintain a high level of cyber security and data privacy protection. The DSCI is a non-profit body and according to Reddy, it will have 25 corporate members from all over the …
The Punekar – http://punekar.in/site/
Controversy in Parliament over cyber security strategy – 25 Jun …
25 Jun 2009
Government launches UK’s first cyber security strategy. New plan will aim to increase risk monitoring and information sharing capabilities 25 Jun 2009. Communications · How government plans for Digital Britain affect UK IT …
The most recent articles from Computing – http://www.computing.co.uk/
[ More results from The most recent articles from Computing ]
Cyber security minister ridiculed over s’kiddie hire plan | Data …
22 hours ago by admin
Security experts have strongly criticised suggestions by a government minister that former hackers might play a key role in Britain’s newly announced cybersecurity strategy.… Offloading malware protection to the cloud …
Data Recovery Moscow – http://www.lexum.ru/
Cyber security chief to be appointed : Industry News : News : BCS
26 Jun 2009
Related Areas. IT Subject Areas. Information on a wide range of IT subjects. Cyber security chief to be appointed. 24/06/2009. A new cyber security tzar is to be appointed by the government to help protect the UK from computer hackers. An announcement from the government regarding the newly created post is expected to be made tomorrow (June 25th). The decision follows an announcement from US president Barack Obama, who is also creating a similar role in his country. …
Latest IT Industry News from BCS – http://www.bcs.org/industrynews
Smart Grid Security Frenzy: Cyber War Games, Worms and Spies, Oh My!
18 Jun 2009 by Katie Fehrenbacher
(NERC) said it has made progress on some “milestones” (more like incremental steps) for smart grid security. NERC says its Board of Trustees has approved the first revisions of its eight cyber security standards, and is working on a second … According to executives at computer security firm IOActive: Studies show that overall project costs are 60 times higher when gaps in information security controls are addressed late in the development cycle, as opposed to projects …
Earth2Tech – http://earth2tech.com/ – References
FIRST FLEET ON. Williams/Nash, Pioneers Australia.: Israel …
28 Jun 2009 by ‘Ric Williams
There was a recent meeting between Homeland Security officials and Israel , including, inter alia, some large international computer firms including Google. Incidentally, Israel has access to all the secret codes of these security systems … A pioneer Israeli counter-terrorism consulting firm, GS-3, is joining forces with ESSI, a U.S. company in the information security field which provides premier cyber- security consulting to government and corporate clients This new …
FIRST FLEET ON. Williams/Nash, Pioneers Australia. – http://williamsfamilyfirstfleeters.blogspot….
Instapundit » Blog Archive » WIRED: Cyber Security Czar Front …
23 Jun 2009 by Glenn Reynolds
WIRED: Cyber Security Czar Front-Runner No Friend of Privacy. “That track record would not put Davis out of the running with Obama, who, after winning his party’s nomination, embraced expanded government wiretapping powers, …
Instapundit – http://pajamasmedia.com/instapundit/ – References
Around The Horn vol.1,129
‘Iceman’ pleads guilty in credit card theft case
By Elinor Mills
Max Ray Vision, aka “Iceman,” pleaded guilty on Monday to two counts of wire fraud stemming from the theft of nearly 2 million credit card numbers and $86 million in alleged fraudulent purchases.
Vision faces up to 60 years …
Michael Jackon Spam/Malware – RIP The King Of Pop
By Darknet on viruses
For people of my age and generation and I’d guess for most readers of Darknet, Michael Jackson would have had a great influence on our lives. The biggest news last week was most certainly his death, as usual the bad guys were extremely quick to capitalize on this and were sending out spam within hours of […]
NAC Appliances Hardest Hit In Network Security By Economic Downturn, Report Says
Infonetics expects a struggling NAC appliance market to rebound big-time by 2013, to nearly $700 million
Botnets Churn Spam, Then Back Again
In Virus and Spyware
Botnets are behind the vast majority of the world’s spam, according to MessageLabs.
Verified Identity Pass shuts down Registered Traveler lanes
Transportation Security Administration declines to comment on closure.
Web Filtering Company Reports Cyber Attack To FBI
The U.S.-based company that claims its programming code was unlawfully included in China’s Green Dam software reports being targeted by a cyber attack.
Sony Begins Shipping PCs With Green Dam Filter
Company beats Chinese government’s July 1 deadline, but Sony disclaims responsibility for any damage caused by the Web filtering software.
Sony Begins Shipping PCs With Green Dam Filter
Company beats Chinese government’s July 1 deadline, but Sony disclaims responsibility for any damage caused by the Web filtering software.
ICANN Names Security Expert As CEO
Rod Beckstrom, former director of the U.S. National Cybersecurity Center, faces demands to make the US organization into an international body.
Generic Rootkit.d Strikes Again in New Variant
By Rachit Mathur on Rootkits and Stealth Malware
A few days ago I got a chance to look at a recent variant of the DNSChanger.ad. It drops a common rootkit that is mostly associated with FakeAlert and DNSChanger Trojans. Over a period of time the dropped sys file names have changed from tdss*.sys to seneka*.sys to skynet*.sys and so on. Our memory detection […]
Symantec culls user data to spot unsafe programs
Symantec is to use the ‘wisdom of the crowds’ and introduce reputation-based security in the next version of its Norton Antivirus 2010 product.
Free tool provides real-time threat information
Intenet backbone company, Interoute has launched a free tool aimed at providing up-to-date information on security threats. The Internet Barometer draws on information provided by 22 sensors placed at strategic points on the Interoute backbone network and gives accurate information on the volume of threats on the Internet at any one time.
DiskShred offers mobile disk destruction service
One company is offering to resolve the perennial problem of how companies can securely dispose of old hard drives containing valuable commercial data, after it setup a mobile disk shredding service that will come to a customer’s site and destroy old hard disks.
Chinese registrars need rapped on knuckles, expert says
A computer security expert is calling for action against two Chinese companies that he and other analysts allege are facilitating spam and cybercrime on the Internet.
Software not smart enough to sort human relationships
Internet search engines and software applications can catalog huge volumes of information, but they aren’t smart enough to trace personal relationships between people, according to the executive chairman of World-Check, a company that maintains a database of individuals that banks and other companies might want to think twice about doing business with.
China bans virtual cash for real-world trade
Peer-to-peer transactions only
Officials in China are banning use of virtual money to buy real-world goods and services.…
Hip-hop site served child porn, police say
Unbeknownst to operator
Police in Switzerland have uncovered a child pornography ring that secretly used a hip-hop website to distribute illegal images to some 2,300 computers in 78 countries.…
Notorious phone phreaker gets 11 years for swatting
End of the (party) line
A notorious phone phreaker has been sentenced to more than 11 years in prison after admitting he took part in a scheme that hacked phone systems to fake emergency 911 calls that sent teams of heavily armed police to the home of unsuspecting victims.…
Mitnick site targeted in DNS attack on webhost
“Mantrained”
A website belonging to security expert Kevin Mitnick was compromised after hackers managed to access a domain name server maintained by the site’s webhost and redirect visitors to pages that displayed pornographic images.…
FTC settles with scareware scammers on reduced terms
10 cents per victim? We’ve spent the rest
US consumer watchdogs at the Federal Trade Commission have agreed to settle a lawsuit against rogue security software distributors on reduced terms.…
Court reinstates ID theft charges in email hack case
Malicious gossip connected to suicide
US judges are grappling with the implications of a workplace email hacking case that led to the suicide of a local official.…
The human factor in laptop encryption
Lock down the business managers!
Hardly a day goes by without news of some laptop containing sensitive information about customers or staff getting lost or stolen. The latest high profile example is the Bord Gais burglary in Dublin in which an unencrypted laptop containing the bank details of 75,000 electricity customers was stolen. Hilariously, Bord Gais told the people affected that “data security and laptop encryption is a major priority for us”. More practically, it urged the names to watch out for their bank accounts.…
Cyber security minister ridiculed over s’kiddie hire plan
‘Naughty boys’ nonsense
Security experts have strongly criticised suggestions by a government minister that former hackers might play a key role in Britain’s newly announced cybersecurity strategy.…
Britney Spears dead hacked
TwitPic exploit suspected in celeb fake obit assault
Britney Spears’s Twitter account has been hacked again – this time around the fake microblogging update falsely reported that the troubled warbler was dead.…
Special SANSFIRE 2009 Podcast Presentations – Mark Hofman, (Mon, Jun 29th)
Our fifth presentation is by one of our Handlers by the name of Mark Hofman. Mark is one of ha …(more)…
Related Searches
Special SANSFIRE 2009 Podcast Presentations – Bojan Zdrnja, (Mon, Jun 29th)
Our fourth presentation is by one of our Handlers by the name of Bojan Zdrnja. Bojan actually …(more)…
New Trojan stealing FTP credentials, attacking FTP websites
By Robert Westervelt
A new Trojan has collected up to 80,000 unique FTP server logins and is injecting malicious code into thousands of FTP websites.
MasterCard increases PCI compliance requirements for some merchants
By Marcia Savage
Company now requires merchants that process one million to six million transactions annually to have onsite assessment by a PCI QSA. Visa says it won’t follow suit.
Motorola Timbuktu Pro Stack Based Buffer Overflow
…
Unisys Business Information Server Stack Buffer Overflow
…
Adobe Shockwave Player Director File Parsing Pointer Overwrite
…
Apple WebKit attr() Invalid Attribute Memory Corruption Vulnerability
…
Cisco Physical Access Gateway Denial of Service Vulnerability
…
Cisco ASA Web VPN Multiple Vulnerabilities
…
Microsoft Office Excel Malformed Records Stack Buffer Overflow (MS09-021)
Remote attackers can exploit this vulnerability by enticing target users to open a malicious Excel file.
Cisco Video Surveillance Products Denial of Service
…
Microsoft Excel Record Parsing Array Indexing Vulnerability (MS09-021)
…
Pivot Cross Site Scripting and HTML Injection
…
Apple Safari File Protocol Handler Information Disclosure and Denial of Service
…
Microsoft Excel String Parsing Integer Overflow Vulnerability (MS09-021)
Successful exploitation allows execution of arbitrary code.
HP OpenView Network Node Manager Execution of Arbitrary Code and DoS
…
IBM AIX ToolTalk Database Server Buffer Overflow Vulnerability
…
How Secure Is Apple`s Snow Leopard for the Enterprise?
NEWS ANALYSIS: Snow Leopard is being touted as a winner in the security space by Apple. But do its features really hold up? With the upcoming release of Microsoft Windows 7, business users might have a better chance to compare the security features of Apple to Microsoft.
– When it comes to the enterprise, security is a constant concern. Most companies have mission-critical data loaded onto employee notebooks walking out the door on a daily basis. At the office, malicious hackers are constantly trying to find ways to break into the network to access that data, ste…
Trojan Swipes FTP Credentials for Major Companies in Malware Attack
Security researchers are tracking a Trojan that has swiped as many as 88,000 FTP credentials for organizations such as Symantec, McAfee, Amazon, Cisco and the Bank of America. According to researchers at Prevx, the compromises are part of an operation that has been in business for more than two years.
– Security researchers have uncovered a cache of stolen FTP credentials belonging to a variety of corporations, including Symantec, McAfee, Amazon and the Bank of America. According to security vendor Prevx, a Trojan has swiped some 88,000 FTP credentials as of this morning. The FTP logins were d…
Veracode Takes Mobile Application Code Analysis to the Cloud
Veracode has added support for Windows Mobile applications to its Web-based code analysis service. Support for other platforms, including Google Android, is on the road map for later this year.
– Veracode has expanded its cloud-based SecurityReview service to help businesses improve security for mobile applications. The service, which analyzes application code for vulnerabilities, is now available for Windows Mobile applications. Support for BlackBerry and Google Android is expected to c…
Brief: Jackson searches resemble attack to Google
Jackson searches resemble attack to Google
Jackson’s death unleashes barrage of online scams (AP)
In technology
AP – Minutes after any big celebrity dies, Internet swindlers get to work. They pump out specially created spam e-mails and throw up malicious Web sites to infect victims’ computers, hoping to capitalize on the sudden high demand for information.
Chinese Registrars Need Rap on Knuckles, Expert Says (PC World)
In technology
PC World – A computer security expert is calling for action against two Chinese companies that he and other analysts allege are facilitating spam and cybercrime on the Internet.
SB09-180: Vulnerability Summary for the Week of June 22, 2009
Vulnerability Summary for the Week of June 22, 2009
Cisco Security Center: IntelliShield Cyber Risk Report
June 22-28, 2009
Report Highlight: Automated Control Systems Risks
FTP login credentials at major corporations breached (CGISecurity.com)
Blind Phone Hacker Gets 11-year Sentence
A blind 19-year-old teenager has been sentenced to more than 11 years in prison for making fake 911 ‘swatting’ calls.
Twitter Gains Upper Hand on Latest Scam
An apparent phishing scam moving through Twitter this week appears to have been halted — but not before numerous users were duped into exposing their information.
Real CEOs Don’t Twitter — Do They?
Top executives typically shun Twitter, Facebook, and other social networks but may be missing a bet, research says.
Edition 1.2 Googled Security Events Corner
Google News Search
US Cyber Command: 404 Error, Mission Not (Yet) Found
Wired News – Noah Shachtman – Jun 26, 2009
(Another: what does a recent and classified National Intelligence Estimate on cyber security recommend.) But already, there’s tough talk in and around the …
Video: Britain launches cyber-terror strategy![]()
ITN NEWS
Britain says facing growing cyber security threat Reuters
Cyber-security strategy launched BBC News
Military Command Is Created for Cyber Security
Wall Street Journal – Siobhan Gorman, Yochi Dreazen – Jun 23, 2009
Maren Leed, a cyber-security expert at the Center for Strategic and International Studies, said the military’s closed computer networks could make it easier …
Gates Creates Cyber-Defense Command Washington Post
New Military Command for Cyberspace New York Times
OSCE ministers seek joint European security policy
eTaiwan News – Nicholas Paphitis, Elena Becatoros – 13 hours ago
AP AP AP AP European countries must cut through a tangle of conflicting policies to build a single voice on security, the Greek OSCE …
FM on OSCE goals ANA
Cyber Security’s Centrality to Internet Issues Discussed At Google
BroadbandCensus.com – Douglas Streeks – Jun 27, 2009
Christopher Painter, director of cyber security for the National Security Council emphasized the importance of cyber security as a national security …
Feds Mulling Incentives for … InternetNews.com
Wide-ranging changes might be sought for cybersecurity Nextgov
Network Shutdown Bill Faces Changes, Aide Says PC World
Cyber-security training mission not coming to Goodfellow
San Angelo Standard Times – Jun 26, 2009
WASHINGTON — A cyber-security training mission isn’t coming to Goodfellow Air Force Base, officials said Friday afternoon. Goodfellow had been in the …
H1N1 flu case reported on Goodfellow Air Force Base San Angelo Standard Times
Ex-DHS Cyber Exec to Head ICANN
GovInfoSecurity.com – Jun 26, 2009
Bernie Thompson, chairman of the House Homeland Security Committee; Motorola Chairman David Dorman; and Electronic Privacy Information Center Executive …
Web IDs agency picks new chief Financial Times
Icann appoints new head honcho V3.co.uk
Md. poised to reap cyber security rewards
Baltimore Sun – Jun 23, 2009
(Baltimore Sun photo by Lloyd Fox / June 11, 2009) Maryland technology companies that specialize in cyber security are expecting to reap the benefit of …
Sourcefire Announces New Security Courses for Dissecting Threats … Business Wire (press release)
Cyber security companies in Maryland getting hot, not bothered Baltimore Sun
Antivirus testing outfit: Microsoft Security Essentials makes the …
TMCnet – Jun 27, 2009
(Network World Middle East Via Acquire Media NewsEdge) Microsoft’s free security software passed a preliminary antivirus exam with flying colors, …
CACI Raises FY 2009 EPS Guidance to $3.09 to $3.16 per Share and …
MarketWatch – Jun 25, 2009
We believe we are well-positioned to win new business in the administration’s high priority areas of cyber security, information technology modernization, …
Security push must include computers
TheNewsTribune.com – 18 hours ago
She consults on cyber security and other national security matters but has no financial stake in the policies advocated here. She wrote this article for The …
Google Blogs Search
The New School of Information Security (Repost)
10 hours ago by admin
Adam Shostack, Andrew Stewart, «The New School of Information Security»Addison Wesley | ISBN: 0321502787 | 2008 | CHM | 288 pages …
FileDownloadFullFileDownloadFull – http://www.filedownloadfull.com/
[ More results from FileDownloadFullFileDownloadFull ]
Information Security and Business Management: The History and …
2 hours ago by admin
Daniil M. Utin, MS, Mikhail A. Utin, Ph.D. Information Security and Business Management: The History and Reality of Misconceptions Preamble. We published an. … New coming security consultant needed a PC on the local network with certain access to network shared drives. It took two months (!) to finally get all things settled. Computer alone took one (!) month to set up. We see here a magic number as two months is actually 60 or so days as in first case. …
TAP | Tech A Peep – http://www.techapeep.com/ – References
Hackers turn gamekeepers for UK cyber security : Security Watch …
26 Jun 2009 by Alan Harten
Hackers turn gamekeepers for UK cyber security. Posted by Alan Harten on Friday, June 26, 2009 · Leave a Comment. The Government is using computer hackers who have reformed, in order to defend Britain and help the county guard against cyber … attacks – the UK Office of Cyber Security to handle policy creations and international prosecutions and the UK Cyber Security Operations Centre which will assess and collate information about threats and possible counterattacks. …
Security Watch – Internet Security News:… – http://www.securitywatch.co.uk/
[ More results from Security Watch – Internet Security News:… ]
Book Video Training: Advances in Information Security and …
19 hours ago by Shytex
Advances in Information Security and Assurance: Third International Conference and Workshops, ISA 2009, Seoul, Korea, June 25-27, 2009. Proceedings (Lecture … Computer Science / Security and Cryptology): Jong Hyuk Park, Hsiao-Hwa Chen …
Book Video Training – http://www.booktraining.net/ – References
[ More results from Book Video Training ]
First Cyber Security Measures Unveiled | TTKN News
27 Jun 2009 by admin
The Prime Minister said the UK’s first national Cyber Security Strategy paves the way for extra funding and new measures to help detect cyber attacks. The. … Mr Brown said the internet and the flow of information has risen dramatically around the world, which has in turn increased the risk. ?Some terrorist groups are using the internet in a wholly exploitative way and of course we have got to beware of any threats to our country.? The PM added: …
TTKN News – http://www.ttkn.com/ – References
Open Rights Group Newsblog : Blog Archive » PM announces Office of …
9 hours ago by Glyn
The PM said an Office of Cyber Security will be formed, and a Cyber Security Operations Centre will provide coordinated protection of critical IT systems from Cheltenham. Mr Brown said the internet and the flow of information has risen …
Open Rights Group Newsblog – http://www.openrightsgroup.org/newsblog/ – References
Internet Security Alliance Updates 6-23-09 : Information Security …
23 Jun 2009
The Department of Homeland Security (DHS) Office of Cybersecurity and Communications (CS&C) National Cyber Security Division (NCSD), the Department of Defense (DoD) and National Institute for Standards and Technology (NIST) Information …
Infosec Update – http://news.mandalorian.com/
[ More results from Infosec Update ]
Schneier on Security: Workshop on Economics of Information Security
24 Jun 2009
June 24, 2009. Workshop on Economics of Information Security. I’m at the 8th Workshop on Economics and Information Security at University College London (field trip to see Jeremy Bentham). Ross Anderson is liveblogging the event. …
Schneier on Security – http://www.schneier.com/blog/ – References
[ More results from Schneier on Security ]
Time for a Cyber NonProliferation Treaty? – Ariel Silverstone’s …
12 hours ago by Ariel
This is the blog of Ariel Silverstone, a globally recognized expert in the fields of risk management and information security. … In contrast to the need to process, create, and securely store ordnance or dual-use items, where the case is Cyber warfare, any and every computer can be, and sometime is, an “instrument of war”. Only in very controlled societies, such as Russia or Iran, can access to computing infrastructure be so restricted as to carefully control who, when, …
Ariel Silverstone» Ariel Silverstone –… – http://arielsilverstone.com/
[ More results from Ariel Silverstone» Ariel Silverstone –… ]
Affordable Web Hosting Information: Website Security Rules Explained
11 hours ago by Affordable Web Hosting Information
Website Security Rules Explained. 2006-2007 has been the years that online shopping has come into its own with online consumers spending a record $65.1 billion in merchandise via the web. More and more people are getting comfortable …
Affordable Web Hosting Information – http://webgatehosting.blogspot.com/
Around The Horn vol.1,128
Internet scareware scammers settle with FTC for $100,000
By jacqui@arstechnica.com (Jacqui Cheng) on security
The Federal Trade Commission has settled a case involving two scareware scammers. The settlement will relieve the two defendants of having to fork over almost $1.9 million as part of a judgment made against them, but will still require them to forfeit $116,697 in assets to the FTC.
The two defendants, James Reno and ByteHosting Internet Services, LLC, were based out of Cincinnati when they began their “massive deceptive advertising scheme.” The two supposedly conned over a million customers into buying computer security software (such as WinFixer, WinAntivirus, DriveCleaner, XP Antivirus, and more) that ended up falsely claiming that they had found viruses, spyware, and porn on people’s machines. The software would then ask for money in order to rid the computers of these fake viruses.
English Microsoft Security Essentials beta filled in <24 hours
By emil.protalinski@arstechnica.com (Emil Protalinski) on Microsoft Security Essentials
This morning, on the Microsoft Security Essentials (MSE) homepage, a message appeared explaining that the limited beta program has already filled up: “Alert! Thank you for your interest in joining the Microsoft Security Essentials Beta. We are not accepting additional participants at this time. Please check back at later a date for possible additional availability.” The MSE beta was released yesterday at around 8am, and less than 24 hours later the English version of the beta was full (MSE was also made available in Brazilian Portuguese). When Ars asked for details, a Microsoft spokesperson explained how quickly the cap was reached:
Watch what Microsoft’s new security app can do
By Seth Rosenblatt
The public beta for Microsoft Security Essentials, the free replacement for Live OneCare, is now closed, but that doesn’t mean you’ve missed your chance to see what it’s like.
In …
Originally posted at The Download Blog
Expert: China’s Green Dam software is unsafe
By Elinor Mills
The content-filtering software the Chinese government wants installed on all PCs sold in that country beginning next week was poorly developed and puts users at risk of having their computers compromised, a security expert who examined the code said on Thursday.
The Chinese government is requiring that all PCs include …
Finjan offers free SecureTwitter browser plug-in
By Elinor Mills
Finally, there’s a tool that can help prevent people from clicking on URLs that appear to come from friends on Twitter and other social media sites but which lead to sites hosting malware.
Web security firm Finjan began offering this week a free browser plug-in dubbed SecureTwitter that warns …
U.K. cybersecurity office to have attack role
By Tom Espiner
The U.K. government plans to form a cybersecurity agency, with functions including cyberattack capability.
The Office of Cyber Security (OCS), dedicated to protecting Britain’s IT infrastructure, will be created with a model proposed–and in part practiced by–the U.S. The U.K. government said Thursday that the OCS …
Green Dam exploit in the wild
By Tom Espiner
An exploit for a flaw in censorware mandated by the Chinese government has been made publicly available for download on the Internet.
The buffer overflow flaw exists in the latest, patched version of Green Dam, 3.17, according to security researcher “Trancer,” who claims authorship of the attack code.
“I …
VC’s automated Twitter feed spreads malware
By Elinor Mills
Updated June 25 at 9:00 a.m. PDTwith Trend Micro saying the Trojan is harmful to Macs and PCs.
Venture capitalist Guy Kawasaki got more than he bargained for from an automated feed he set up on his Twitter account. …
Microsoft’s free security beta fills up
By Ina Fried
A day after making a beta of its free security program available, Microsoft has said it already has the number of testers it needs and has halted new downloads.
(Credit: CNET)
Well, that didn’t take long.
A day after making available a free beta of its Microsoft Security Essentials …
Originally posted at Beyond Binary
Q&A: Adrian Lamo, the hacker philosopher
By Elinor Mills
…
Abbreviate Me Two Times (I’m Gone Away)
By Rik Ferguson on web
A quick warning note. I am starting to see URLs being shortened with one service, and then shortened again with a second service in order to overcome URL previewing solutions. In fact, if you came here as a result of my tweet about this blog entry, you came through three URL shorteners. Here’s an innocuous example that […]
Would the Real Cybersecurity Minister Please Stand Up.
By Rik Ferguson on government
Let me get this out of the way first, this blog always represents my own opinion, and not Trend Micro’s official view. Yesterday I made a posting about the release of the UK government’s National and Cyber Security Strategy documents. I spent some time talking to the press and broadcast media and one of the recurring […]
What Can We Expect from a National Security Strategy?
By Rik Ferguson on government
UPDATE: The strategy update has been published, at first glance, it appears to hit several of the points I mentioned below. I will publish my thoughts on the content later this afternoon. I did note though, from a BBC report “Officials said it would require input from those who had their own expertise in hackers. “We need […]
Targeted Attack Designed to Infect Both Macs and PCs.
By Rik Ferguson on web
UPDATE (25th June): Guy Kawasaki has stated that his Twitter account was not compromised, the malicious tweet came from a feed that Guy’s account is subscribed to automatically post. The feed comes from NowPublic, a user generated news feed. According to the Wall Street Journal “Michael Tippett, co-founder of NowPublic, responds, pointing out that Mr. […]
BackTrack 4 Pre Release Available For Download
By Darknet on wireless security livecd
You may remember back in February the BETA of BackTrack 4 was released for download, the team have made many changes and have now released BackTrack 4 Pre Release. For those that don’t know BackTrack is the top rated linux live distribution focused on penetration testing. With no installation whatsoever, the analysis platform is started directly […]
Database Security: The First Three Steps
A guide to locating sensitive data in databases — and finding a strategy to protect it
Booming Underground Economy Makes Spam A Hot Commodity, Expert Says
Booming underground markets make spam even easier and more lucrative than before, researcher says
FTC Issues Final Order In CVS Caremark Data Security Case
FTC issues final order censuring CVS Caremark for mishandling customer data
Attackers Use Michael Jackson, Farrah Fawcett as Lure
In Virus and Spyware
Spammers are taking advantage of reports on the deaths of celebrities Michael Jackson and Farrah Fawcett to infect users with malware.
Global Takeout: China Cooking Up Lots of Spam
In Virus and Spyware
Researchers contend that China is currently accounting for as much as 70 percent of the world’s unsolicited e-mail.
Apps Whitelisting Proponents Tout Growing Acceptance
In Vulnerability Research
Applications whitelisting vendors maintain that the current malware environment and demand for tools to address the shortcomings of traditional AV are speeding their push to market.
Twitter Malware Attack Targets Both Mac and PC
In Trojan attacks
Attackers hijacked the Twitter account of venture capitalist and ex-Apple evangelist Guy Kawasaki in a bid to lure users to a site hosting a Trojan. The catch — the malware affects both Windows PCs and Apple Mac computers.
Britain to establish new cybersecurity office
The British government is establishing a new Office of Cyber Security, as part of a broader strategy dedicated to protecting Britain’s information technology infrastructure.
Alexander: Military cybersecurity requires broaders training
The man expected to head the new military cyber command says military cybersecurity efforts require broader-based training and improved support mechanisms for the military services, while also preserving civil liberties.
Napolitano endorses PASS ID bill
Homeland Security Secretary Janet Napolitano has backed proposed legislation that would repeal part of the Real ID Act.
Cyber Command: Observers worry about unintended consequences
The size and importance of DOD’s military operations have caused some observers to wonder about how big an effect the Cyber Command might have outside its own domain.
House backs biometrics in DHS 2010 spending bill
The House endorsed a spending increase on DHS’ largest biometrics program in the fiscal 2010 spending bill it has passed.
DOD creates Cyber Command as U.S. Strategic Command subunit
The director of NSA will lead the U.S. Cyber Command, which will be a subunit of the U.S. Strategic Command and will reach initial operating capacity in October.
ICANN Names Security Expert As CEO
Rod Beckstrom, former director of the U.S. National Cybersecurity Center, faces demands to make the US organization into an international body.
Most PC Users Have A Dozen Dangerous Apps
The average PC user has a dozen unpatched applications installed.
Defense Secretary Orders Cyberspace Command
Initiative aims to unify offense and defense in cyberspace under U.S. military command and enable responses “in Internet time rather than bureaucratic time.”
Defense Secretary Orders Cyberspace Command
Initiative aims to unify offense and defense in cyberspace under U.S. military command and enable responses “in Internet time rather than bureaucratic time.”
Green Dam Deadline Remains Unchanged Despite U.S. Objections
Chinese authorities claim that putting Green Dam censorware on all new PCs sold in the country is necessary to limit young people’s exposure to “harmful information.”
Michael Jackson News Affects Web Traffic
By Paula Greve on Web and Internet Safety
The announcement of Michael Jackson’s death has caused immediate effects on the Web 2.0 world. The impact ranged from the interruption on Facebook of coverage of Farrah Fawcett’s death to a surge experienced by Twitter. The Web 2.0 world is definitely abuzz with traffic regarding his passing. Within hours the percentage of “long-tail” URL traffic associated with […]
Bad News Offers Opportunity to Spread Malware
By Guilherme Venere on Web and Internet Safety
With the current news about the deaths of Farrah Fawcett and Michael Jackson, it’s a good idea to remind our readers to beware of blackhat attempts to distribute malware to anyone looking for news. Every time a disaster happens or news about some celebrity reaches the media, malware writers try to take advantage of it. […]
China remains spam haven due to ‘bulletproof’ hosting
An overwhelming majority of Web sites promoted through spam are hosted in China at service providers that many times choose to ignore complaints and allow illegal activity, according to research from the University of Alabama.
Michael Jackson spam spreads, malware attacks likely
Within hours of the death of Michael Jackson’s death, spam capitalizing on his demise hit inboxes, a security firm said today as it warned that more was in the offing.
Fake Online Harry Potter Movies Launch Malware Attack
If you happen to see a too-good-to-be-true offer to watch the latest Harry Potter movie online for free, watch out.
Network shutdown bill faces changes, aide says
A bill in the U.S. Senate that would allow President Barack Obama to shut down parts of the Internet during a cybersecurity crisis will likely be rewritten and needs input from private businesses, said a congressional staff member associated with the legislation.
Security Experts Visualize Botnets With Eye On Defense
Not all botnets are organized in the same way. That’s the conclusion of a report from Damballa which seeks to categorize the dominate structures. It attempts to explain why certain types of blocking and filtering will work against some botnets, and not for others.
Michael Jackson Death Spurs Spam, Viruses
Less than 24 hours after Michael Jackson’s death, fraudsters are exploiting public interest with their attempts to spread spam and malware. Security researchers say they’ve observed hundreds of cases of malicious messages masquerading as information about Jackson’s death. Some of them, they say, popped up within minutes of the news.
FTC suspends heavy penalty against scareware defendants
The U.S. Federal Trade Commission has suspended the majority of a judgment levied against two defendants accused of selling bogus security software to up to a million consumers.
Sophos warns of Michael Jackson spam emails
Hackers are using Michael Jackson’s death to try and trick people into disclosing personal details, says Sophos.
Security agencies to combat cyber attacks, PM announces
Intelligence agents and computer experts are to step up operations against a growing online threat from “criminals, terrorists and hostile states”, as part of the government’s updated national security strategy.
Out of business, Clear may sell customer data
Three days after ceasing operations, owners of the Clear airport security screening service acknowledged that their database of sensitive customer information may end up in someone else’s hands, but only if it goes to a similar provider, authorized by the U.S. Transportation Security Administration.
Facebook puts privacy controls in users’ hands
Facebook has updated its Publisher tools to give users more control over who gets to see their posts on the social network.
Infosys chairman to head government identity project
Infosys Technologies’ co-chairman, Nandan Nilekani, has quit his post to take up a position with the Indian federal government, with the rank of a cabinet minister.
Microsoft Security Essentials: The First Test Results Are In
The biggest question on everyone’s minds with regard to Microsoft Security Essentials is how well it can detect and remove malware. The early returns are in, and Microsoft Security Essentials performed well overall in initial malware detection testing provided to PC World by AV-test.org.
Merchants Struggle to Comply With PCI Security In Economy
The heads of seven business organizations sent PCI Security Standards Council General Manager Bob Russo a cry for help earlier this month, saying the recession is making it “increasingly difficult” for merchants to meet the requirements of the Payment Card Industry’s Data Security Standard (PCI DSS).
Yet Another Malware Attack Spreads via Twitter
Guy Kawasaki — a Silicon Valley venture capitalist who was partially responsible for marketing the Macintosh in 1984 — has almost 140,000 Twitter followers. Many of those followers likely thought it was strange that Kawasaki was suddenly into shilling porn, when a link purporting to host a pornographic video of “Gossip Girl” star Leighton Meester appeared on June 23. Anyone who downloaded the video discovered a virus that ravaged both PCs and Macs.
National Grid signs £207m deal for data network
National Grid has signed £207 million worth of deals with Cable & Wireless for a new data network.
Webroot: social networkers open to ID theft
A third of social networkers have at least three pieces of information visible on their profiles that could make them vulnerable to ID theft, says Webroot.
Online banking device reads information from a screen
As German banks layer more security into their online banking procedures, security vendor Gemalto has launched a device it says makes completing transactions easier.
Windows installs updates without permission, researchers say
Windows is installing “surprise updates” against the wishes of some users, who have expressly set up the operating system not to deploy patches without permission, researchers charged today.
TJX reaches $9.75 million breach settlement with 41 states
TJX Companies has agreed to pay for investigations by 41 states into a massive data breach that gave hackers access to data stored on as many as 94 million payment cards used by TJX customers.
Securely wipe your hard drive
Reader Jim Bradley seeks a way to securely wipe the data from his hard drive. He writes:
Reporters find Northrop Grumman data in Ghana market
A team of journalists investigating the global electronic waste business has unearthed a security problem too. In a Ghana market, they bought a computer hard drive containing sensitive documents belonging to U.S. government contractor Northrop Grumman.
Experts Only: Time to Ditch the Antivirus?
To the average IT security practitioner, the idea of disabling antivirus on new machines might seem blasphemous. After all, weren’t we all told in IT Security 101 that everyone needs AV to keep the malware and data thieves at bay?
Unique cloud features can improve cloud security
Cloud computing may offer a new form of data defense by bringing into play the maneuverability of data to secure it from attacks while the source of the attack can be pinpointed and neutralized, a blogger suggests.
Subtle pressures for security policy compliance
Information security officers and managers are constantly looking for ways to encourage colleagues to comply with security policies. The paper “Social Psychology and INFOSEC: Psycho-Social Factors in the Implementation of Information Security Policy” summarizes a number of principles from social psychology that can help practitioners in our work.
MS Security Essentials: Basic Protection
Microsoft today released a limited beta version of Microsoft Security Essentials, a free antivirus application for users of Windows XP, Vista, or 7. The new app, which will replace Windows Live OneCare, aims to cover the basic security needs of home users, and its easy-to-use interface appears to be taking the right approach to the task.
High profile Twitter hack spreads porn Trojan
Former Apple Macintosh evangelist Guy Kawasaki [cq] posts Twitter messages about a lot of different thing, but the message he put up on Tuesday afternoon was really out of character.
E-Mail Crooks Target Webmail Accounts
Imagine having to explain an e-mail message that asks your friends for money–a message sent from your Webmail account. (Webmail refers to any e-mail service you use via a Web browser rather than through an e-mail client.) That’s exactly what’s happening: Scammers are breaking into such accounts and, from those addresses, sending e-mail messages to the victims’ entire contact list. The messages often tout a Web site (such as an e-commerce site), or even ask for money directly.
Abrupt closure of airport fast-lane program sparks concern over customer data
A company that collected detailed personal information including biometric data on 260,000 individuals as part of a registered air traveler program it operated has abruptly gone out of business, leaving many customers wondering about the safety and privacy of their personal data.
Defense Secretary Gates approves creation of U.S. Cyber Command
Defense Secretary Robert Gates today approved the creation of a unified U.S. Cyber Command to oversee the protection of military networks against cyber threats.
Adobe issues update for Shockwave Player
Adobe Systems has released a patch for its Shockwave Player to fix a critical vulnerability, the company wrote on its security blog on Tuesday.
Related Searches
Police to create regional e-crime squads
Police forces across the UK are to collaborate to create regional cybercrime squads.
UK shut out for Microsoft Security Essentials
Microsoft’s new free antivirus product – Microsoft Security Essentials – is now available in beta, but not if you live in the UK.
Related Searches
Phoenix Freeze Auto-Locks Laptops via Smartphone
A new product from Phoenix Technologies, called Freeze, lets you use BlackBerry or iPhone Bluetooth to tell a PC that you’re leaving the area and want it to lock up. When you return, Phoenix Freeze can also automatically unlock the machine so it’s ready for you. However, it only works on Windows PCs, doesn’t support 64-bit platforms, disables all other Bluetooth peripherals and seems to be a bit buggy for an official release.
Titsup airport express lane biz may pawn flyer data
If the feds Clear it
Defunct American airport security lane service Clear said on Friday it may sell its sensitive customer data to a similar provider if it’s authorized to do so by the US government.…
Blue chip FTP logins found on cybercrime server
Monster breach exposes Amazon and BBC to compromise
Security researchers have found a treasure chest of FTP passwords, some from high profile sites, on an open cybercrime server.…
ICANN appoints former cybersecurity chief as new boss
Provocative pick
Internet oversight agency ICANN has hired former US cybersecurity chief Rod Beckstrom as its next boss.…
Spammers swift to exploit Jackson death to punt malware
Who’s bad?
Updated Miscreants have wasted no time exploiting the shock death of Michael Jackson to run email harvesting and banking Trojan campaigns.…
Louisiana judge holds Dell in contempt
Dell making a ‘mockery’ of system in New Orleans brouhaha
A Louisiana judge found Dell in contempt of court Thursday after berating the eponymous computer vendor for making a “mockery” of the system though haphazard retrieval of evidence for a lawsuit that alleges corruption in the city of New Orleans’ crime-camera program.…
Defense-contract discs sold in African market for $40
Northrop Grumman and Pentagon data dumped
Dumped hard drives with US defense data have turned up for open sale in a West African market.…
US calls for China to revoke censorware plan
Green Dam under attack
The US adminstration is pushing China to review its controversial policy of mandating the installation of specific content filtering software on new PCs.…
Crypto guru urges incentives for SSL cert recall
Come in MD5, your time is up
An SSL security guru is urging incentives to promote website certificate upgrade in response to problems with a widely-used digital-signature algorithm.…
UK.gov decides best form of cyber defence is attack
Playing the great game online
UK cyber security spooks will soon have the ability to undertake proactive missions online rather than just playing defense, under the revamped National Security Strategy published today.…
Chrome update plugs hush-hush browser hole
As Secunia releases browser patching tool
Google has pushed out a new version of its browser that protects against a critical vulnerability as well as fixing some stability snags.…
Microsoft cuts off Security Essentials downloads
Less than a day later
Redmond has cut off access to its Microsoft Security Essentials beta, less than a day after offering the free security app to John Q. Public on a first-come, first-served basis.…
MS no-frills security scanner gets thumbs up in early tests
Security Essentials does what it says on the tin
Microsoft’s limited but free-of-extra-charge anti-malware scanner has performed creditably in early tests.…
US military cyberwar force will work with NSA
Priority is net ‘defense’. As in Department of Defense
The long wrangle among the US military about who gets to be in charge of cyber warfare and who gets all the resulting pork appears to have been settled. Questions remain, however, regarding the level of America’s readiness to take offensive military cyber action against enemies presumably overseas.…
Homebrew Pre apps find easy install
We’ve got ourselves a security hole, Rubber Duck
Developers unwilling to wait for the Mojo SDK for Palm’s Pre, or to be bound by its restrictions, have discovered that unsigned applications can be installed using a specially-formatted e-mail rather than any mucking about with unlocking the handset.…
UK police chiefs mull regional cybercrime squads
We’re the eSweeney son, and we ain’t had any dinner
British police chiefs are drawing up plans to set up regional “cybercrime” squads along the lines of existing teams tasked to handle anti-terror operations.…
Inside a Phish
Categories: Case Studies,Malicious Code
Paper Added: June 25, 2009
IP Address Range Search with libpcap, (Sun, Jun 28th)
This week, I received a request to search for a range of destination addresses that cannot easily do …(more)…
New NIAP Strategy on the Horizon, (Sat, Jun 27th)
It has been recently announced that the Common Criteria Evaluation and Criteria Scheme (CCEVS) will …(more)…
Special SANSFIRE 2009 Podcast Presentations – State of the Internet Panel, (Fri, Jun 26th)
Our third presentation is by all of the Internet Storm Center Handlers that were present (at the tim …(more)…
Michael Jackson Spam Distributes Malware, (Fri, Jun 26th)
As we anticipated in our yesterday’s diary, spammers are starting to exploit attention-grabbing head …(more)…
How Malware Defends Itself Using TLS Callback Functions, (Fri, Jun 26th)
Malware authors employ numerous and creative techniques to protect their executables from reverse-en …(more)…
Michael J & Farrah F death SPAM, (Thu, Jun 25th)
With the reported death of Farrah Fawcett and Michael Jackson today, it is likely only a matter of h …(more)…
PHPMYADMIN scans, (Fri, Jun 26th)
We have received some reports (thanks Drew) of scanning for keyhandler.js which is part of PHPMyAdmi …(more)…
Special SANSFIRE 2009 Podcast Presentations – John Bambenek, (Thu, Jun 25th)
Our second presentation is by one of our Handlers by the name of John Bambenek. You may recogn …(more)…
Special SANSFIRE 2009 Podcast Presentations – Deb Hale, (Thu, Jun 25th)
Recently at SANSFIRE 2009, there were a lot of talks given by our Internet Storm Center Handlers.&nb …(more)…
TCP scanning increase for 4899, (Wed, Jun 24th)
An observant reader reports that he is seeing a very noticeable increase in TCP scanning for port 48 …(more)…
Exploit tools are publicly available for phpMyAdmin, (Wed, Jun 24th)
As a follow-up to our earlier diary about phpMyAdmin scanning, there is at least 2 exploits posted i …(more)…
Adobe Shockwave Player Update, (Wed, Jun 24th)
Several readers pointed out that Adobe released a security update for the Shockwave Player today whi …(more)…
Five Guilty Pleas in Stock Manipulation Spam Case (June 25, 2009)
Five people have pleaded guilty to charges related to a spam scheme that artificially inflated the price of Chinese penny stocks…….
Hard Drive Purchased in Ghana Contains US Military Contractor Data (June 24 & 25, 2009)
Canadian journalism students bought a hard drive for US $40 at a market in Ghana, only to discover that it contained unencrypted information about contracts between military contractor Northrop Grumman and the Pentagon…….
Conference on Cyberwarfare Attendees Discuss Pros and Cons of Proactive Attacks (June 21, 2009)
People attending the Conference in Cyber Warfare in Tallinn, Estonia discussed the merits and drawbacks of conducting proactive cyber attacks…….
Payment Card Industry Security Standards Council Seeks Input (June 24 & 25, 2009)
The Payment Card Industry Security Standards Council (PCI SSC) is seeking “detailed and actionable feedback” from member organizations on versions 1…….
Customers Worry About Defunct Registered Traveler Program Data Security (June 23, 2009)
Customers of the suddenly-defunct Verified Identity Pass (VIP) registered air travel service Clear have expressed concern about the security of the data they provided to the company…….
Adobe Issues Shockwave Update to Fix Vulnerability (June 23, 24 & 25, 2009)
Adobe has released an update for a critical flaw in its Shockwave Player…….
Stolen Laptop Holds Cornell University Staff and Student Data (June 24, 2009)
Cornell University in Ithaca, NY has notified approximately 45,000 current and former staff members, students and their dependents that a stolen laptop computer contains their unencrypted, personally identifiable information…….
Green Dam Exploit Posted to Internet (June 25, 2009)
An exploit for a buffer overflow in the controversial Green Dam Youth Escort filtering software has been released in the wild…….
TJX Agrees to $9.75 Million Settlement (June 23, 2009)
TJX, parent company of TJ Maxx and Marshalls, has agreed to a US $9…….
Security Maxims
Smile ruefully in recognition at this list of security maxims, including “The Ignorance is Bliss Maxim: The confidence that people have in security is inversely proportional to how much they know about it…….
Gates Orders Creation of Unified Military Cyber Command (June 23 & 24, 2009)
US Defense Secretary Robert Gates has given the official go-ahead to the creation of a unified military cyber command dedicated to managing Pentagon cyber warfare and network defense efforts…….
UK Releases National Security Strategy (June 25, 2009)
According to the recently released National Security Strategy, the UK government plans to establish a new cyber security agency called the Office of Cyber Security (OCS) that will manage the government’s cyber security program and act as a hub for information sharing between the public and private sectors…….
Microsoft Limits Security Essential Beta Downloads to 75,000 (June 23 & 24, 2009)
Microsoft has halted downloads of its free Microsoft Security Essentials beta software…….
Man Arrested for Stealing and Selling Client Data (June 25 & 26, 2009)
Police in Tokyo have arrested Hideaki Kubo, a former Mitsubishi UFJ Securities Co…….
Social engineering training could disrupt botnet growth
By Brian Sears
Security pros should address social engineering attacks with end users, helping them identify the tactic and possibly have an impact on botnet viability.
TJX to pay $9.75 million for data breach investigations
By Robert Westervelt
The company agrees to pay legal expenses related to investigations conducted by 41 Attorneys Generals and establish a data security fund for states.
Will the Antivirus Market Be Challenged or Complimented By Whitelisting?
Application whitelisting is being talked up by everyone from pure-play vendors like CoreTrace to larger security vendors like McAfee and Symantec. But while many say a hybrid blacklist/whitelist approach is needed, CoreTrace is positioning itself as an alternative to blacklist-based anti-virus.
– There has been plenty of talk in the past year or so among anti-virus vendors about the usefulness of application whitelisting. But when it comes to the question as to whether or not the technology can replace anti-virus, the subject gets a bit stickier. Whitelisting allows a list of approved file…
Facebook Tightens Privacy Controls
A beta version of Facebook’s publisher gives users more control over who can see their content. The move is meant to improve security and privacy on the social networking site.
– Facebook is testing out granular privacy controls for its users that will allow them to exercise more control over who sees published content. Just recently, Facebook made a beta version of its publisher available to some of its users that allows them to configure the settings for who can view …
IBM Discovers Encryption Scheme That Could Improve Cloud Security, Spam Filtering
A researcher at IBM reports having developed a fully homomorphic encryption scheme that allows data to be manipulated without being exposed. Researcher Craig Gentry’s discovery could prove to be important in securing cloud computing environments and fighting encrypted spam.
– An IBM researcher has uncovered a way to analyze data while it is still encrypted, in what could be a boon for both spam-filtering applications and cloud computing environments. The challenge of manipulating data without exposing it has bugged cryptographers for decades. But in a breakthrough, …
Enterprise Security: Educate Employees or Leave It to Microsoft?
NEWS ANALYSIS: How much does enterprise security really matter? Since most employees aren’t being educated, it might not matter enough to businesses. For many companies, using software such as Microsoft Security Essentials makes more sense since employee computers are protected and IT departments can save time and money by not having to train employees about security.
– Quite a few security issues have impacted the business world over the past few months. The Conficker worm was considered a possibly damaging issue. The Nine Ball outbreak looked like it had the potential of unleashing some serious damage on the enterprise after it compromised 40,000 legitimate Web…
Cisco Baking RSA Data Loss Prevention Technology Into Its E-mail Security Mix
Cisco plans to integrate DLP technology from EMC’s RSA security division into some of its IronPort e-mail security appliances by the fall. The integration is the result of a partnership between RSA and Cisco that was announced last year at the RSA security conference.
– EMC s RSA security division is bringing its data loss prevention technology to bear in the e-mail security space through integration with Ciscos IronPort appliances. By the fall, the DLP (data loss prevention) technology from RSA will be built into the Cisco IronPort C-Series applian…
U.S. Defense Secretary Orders Creation of Cyber Command
U.S. Secretary of Defense Robert Gates has ordered the creation of a new command to unify efforts at the Pentagon to secure military networks. Plans for the Cyber Command come a month after President Obama declared cyber-security a national security priority in a speech.
– U.S. Secretary of Defense Robert Gates has ordered the creation of a Cyber Command to help secure the U.S. military’s computer networks, according to reports. In a memo, Gates said he will recommend President Barack Obama put the director of the National Security Agency in charge of the com…
Ex-DHS Cyber Chief Tapped as President of ICANN
In U.S. Government
Former Department of Homeland Security cyber chief Rod A. Beckstrom has been tapped to be the new president of the Internet Corporation for Assigned Names and Numbers (ICANN), the California based non-profit, which oversees the Internet’s address system. Most recently, Beckstrom was director of the National Cyber Security Center — an organization created to coordinate security efforts across the intelligence community. Beckstrom resigned that post in March, citing a lack of funding and authority. Beckstrom joins ICANN as the Internet governance body faces some of the most complex and contentious proposed changes to the Internet’s addressing system in the organization’s entire 11-year history. For example: — The United States is under considerable pressure to give up control over ICANN and turn it over to international supervision and management. ICANN currently operates under a Joint Project Agreement with the U.S. government, but that agreement is due to expire at the end
Critical Security Fix for Adobe Shockwave Player
In New Patches
Adobe Systems Inc. on Tuesday issued a software update to fix a critical security flaw in its Shockwave Player, a commonly installed Web browser plug-in. According to Adobe, a malicious or hacked site could use the security hole to install malicious software if the visitor merely browses the site with a vulnerable version of the media player software. The flaw exists in Shockwave Player (also known as Macromedia Shockwave Player) version 11.5.0.596 and earlier. To find out whether Shockwave is installed and which version may be on your PC, visit this site. In a posting to its security blog, Adobe said it is not aware of any exploits in the wild for this vulnerability. Adobe recommends Shockwave Player users on Windows uninstall Shockwave version 11.5.0.596 and earlier on their systems, restart and install Shockwave version 11.5.0.600, available here. Readers should be aware that by default this patch will also try
Microsoft Debuts Free Antivirus Software Beta
In Safety Tips
Microsoft on Tuesday released a beta version of its new free anti-virus offering, Microsoft Security Essentials (a.k.a “Morro”). My review, in short: the program is a fast, easy to use and unobtrusive new addition to the stable of free anti-virus options available today. MSE is basically the next generation of Microsoft’s Windows Live Onecare anti-virus and anti-spyware service, but without all of the extras, such as a firewall, data backup solution or PC performance tuning (Microsoft announced in Nov. 2008 that it would stop selling Onecare through its retail channels at the end of June 2009). The toughest part was getting the program installed. MSE can run on Windows XP, Vista or Windows 7 (both 32-bit and 64-bit versions), but it failed to install on an XP Pro system I tried to use as my initial test machine — leaving me with nothing more than a failure message and cryptic
Brief: Adobe re-patches Shockwave player
Adobe re-patches Shockwave player
Brief: Pentagon signs off on Cyber Command
Pentagon signs off on Cyber Command
Simpler IP Range Matching with Tshark Display Filters
By Richard Bejtlich
![]() In today’s SANS ISC journal, the story IP Address Range Search with libpcap wonders how to accomplish the following:
In today’s SANS ISC journal, the story IP Address Range Search with libpcap wonders how to accomplish the following:
…how to find SYN packets directed to natted addresses where an attempt was made to connect or scan a service natted to an internal resource. I used this filter for addresses located in the range 192.168.25.6 to 192.168.25.35.
The proposed answer is this:
tcpdump -nr file '((ip[16:2] = 0xc0a8 and ip[18] = 0x19 and ip[19] > 0x06)\
and (ip[16:2] = 0xc0a8 and ip[18] = 0x19 and ip[19]
I am sure it’s clear to everyone what that means!
Given my low success rate in getting comments posted to the SANS ISC blog, I figured I would reply here.
Last fall I wrote Using Wireshark and Tshark display filters for troubleshooting. Wireshark display filters make writing such complex Berkeley Packet Filter syntax a thing of the past.
Using Wireshark display filters, a mere mortal could write the following:
tshark -nr file 'tcp.flags.syn and (ip.dst > 192.168.25.6 and ip.dst
Note that if you want to be inclusive, change the > to >= and the
To show that my filter works, I ran the filter against a file with traffic on my own 192.168.2.0/24 network, so I altered the last two octets to match my own traffic.
$ tshark -nr test.pcap 'tcp.flags.syn and (ip.dst > 192.168.2.103 and ip.dst
137 2009-06-28 16:21:44.195504 74.125.115.100 -> 192.168.2.104 HTTP Continuation or non-HTTP traffic
You have plenty of other options, such as ip.src and ip.addr.
Which one do you think is faster to write and easier to understand?
Richard Bejtlich is teaching new classes in Las Vegas in 2009. Regular Las Vegas registration ends 1 July.
Copyright 2003-2009 Richard Bejtlich and TaoSecurity (taosecurity.blogspot.com and www.taosecurity.com)
Effective Digital Security Preserves Long-Term Competitiveness
By Richard Bejtlich
Yesterday I mentioned a speech by my CEO, Jeff Immelt. Charlie Rose also interviewed Mr Immelt last week. In both scenarios Mr Immelt talked about preserving long-term competitiveness. Two of his themes were funding research and development and ensuring the native capability to perform technical tasks.
Black Hat Budgeting
By Richard Bejtlich
Earlier this month I wondered How much to spend on digital security. I’d like to put that question in a different light by imagining what a black hat could do with a $1 million budget.
The ideas in this post are rough approximations. They certainly aren’t a black hat business plan. I don’t recommend anyone follow through on this, although I am sure there are shops our there who do this work already.
Being a Critic Is Easy, So What Would I Do?
By Richard Bejtlich
After my last post, some of you are probably thinking that it’s easy to be a critic, but what would I suggest instead? The answer is simple to name but difficult to implement.
Ugly Security
By Richard Bejtlich
I read Anton Chuvakin’s post MUST READ: Best Chapter From “Beautiful Security” Downloadable! with some interest. He linked to a post by Mark Curphey pointing out that Mark’s chapter from O’Reilly’s new book Beautiful Security was available free for download in .pdf format. O’Reilly had been kind enough to send me a copy of the book, so I decided to read Mark’s chapter today.
I found the following excerpts interesting.
DoD Creates USCYBERCOM
By Richard Bejtlich
 Today is an historic day for our profession, and for my American readers, our country. As reported in The Washington Post and by several of you, today Secretary Gates ordered the creation of U.S. Cyber Command, a subordinate unified command under U.S. Strategic Command. The NSA Director will be dual-hatted as DIRNSA and CYBERCOM Commander, with Title 10 authority, and will be promoted to a four-star position. Initial Operational Capability for CYBERCOM is October 2009 with Full Operational Capability planned for October 2010. Prior to CYBERCOM achieving FOC, the Joint Task Force – Global Network Operations (JTF-GNO) and the Joint Task Force – Network Warfare (JTF-NW) will be “disestablished.”
Today is an historic day for our profession, and for my American readers, our country. As reported in The Washington Post and by several of you, today Secretary Gates ordered the creation of U.S. Cyber Command, a subordinate unified command under U.S. Strategic Command. The NSA Director will be dual-hatted as DIRNSA and CYBERCOM Commander, with Title 10 authority, and will be promoted to a four-star position. Initial Operational Capability for CYBERCOM is October 2009 with Full Operational Capability planned for October 2010. Prior to CYBERCOM achieving FOC, the Joint Task Force – Global Network Operations (JTF-GNO) and the Joint Task Force – Network Warfare (JTF-NW) will be “disestablished.”
As one of my friends said: “Step one to your Cyber Service — what will the uniforms look like?”
Richard Bejtlich is teaching new classes in Las Vegas in 2009. Regular Las Vegas registration ends 1 July.
Copyright 2003-2009 Richard Bejtlich and TaoSecurity (taosecurity.blogspot.com and www.taosecurity.com)
US, Russia in dispute over computer attacks: report (AFP)
In politics
AFP – Less than two weeks before President Barack Obama’s visit to Moscow, the United States and Russia cannot agree how to counter the growing threat of cyberwar attacks that could wreak havoc on computer systems and the Internet, according to The New York Times.
Michael Jackson Death Spurs Spam, Viruses (PC World)
In technology
PC World – Less than 24 hours after Michael Jackson’s death, fraudsters are exploiting public interest with their attempts to spread spam and malware. Security researchers say they’ve observed hundreds of cases of malicious messages masquerading as information about Jackson’s death. Some of them, they say, popped up within minutes of the news.
Fake Online Harry Potter Movies Launch Malware Attack (PC World)
In technology
PC World – If you happen to see a too-good-to-be-true offer to watch the latest Harry Potter movie online for free, watch out.
FTC OKs $1.9M Deal Over Deceptive ‘Scareware’ Ads (PC Magazine)
In technology
PC Magazine – The Federal Trade Commission has reached a $1.9 million settlement with two defendants who allegedly operated a deceptive advertising scheme to dupe consumers into buying computer security products.
SaaS, Not Shopping, Is Focus of Symantec’s New CEO (PC World)
In technology
PC World – CIOs think of Symantec as a company that buys its way into new markets. Over the past decade the Cupertino, California, vendor has snatched up about 30 companies as it’s evolved from an antivirus and tools seller to an aspiring enterprise infrastructure vendor.
Security Essentials Does Its Job With No Frills (PC World)
In technology
PC World – People often turn to me for advice regarding what anti-virus package to get. Usually I recommend McAfee or AVG, but Security Essentials will be my go-to anti-malware package once it’s released from beta. For small-business and home users, the price, performance, and ease-of-use of MSE can’t be beat.
Yet Another Malware Attack Spreads via Twitter (PC World)
In technology
PC World – Guy Kawasaki — a Silicon Valley venture capitalist who was partially responsible for marketing the Macintosh in 1984 — has almost 140,000 Twitter followers.
UK looks to young geeks to secure cyberspace (AP)
In technology
AP – Britain is hiring former computer hackers to join a new security unit aimed at protecting cyberspace from foreign spies, thieves and terrorists, the country’s terrorism minister said.
Panda Outlines 2010 Security Lineup (PC Magazine)
In technology
PC Magazine – When it comes to computer security, you usually want as much as you can get. But that doesn’t mean you want that protection to affect everything else you do on your PC. With that in mind, Panda Security has devised its 2010 lineup of security packages.
Britain says facing growing cyber security threat (Reuters)
In technology
Reuters – Britain warned on Thursday of a growing risk to military and business secrets from computer spies and pledged to toughen cyber security to protect the 50 billion pounds ($82 billion) spent a year online in its economy.
Microsoft Security Essentials: The First Test Results Are In (PC World)
In technology
PC World – The biggest question on everyone’s minds with regard to Microsoft Security Essentials is how well it can detect and remove malware. The early returns are in, and Microsoft Security Essentials performed well overall in initial malware detection testing provided to PC World by AV-test.org.
Pro-Iranian regime hackers invade Oregon computers (AP)
In us
AP – Hackers defaced the home page of the Oregon University System, posting a caustic message telling President Barack Obama to mind his own business and stop talking about the disputed Iranian election.
Vulnerabilities in Cisco Video Surveillance Products
In Cisco Security Advisory
Cisco Physical Access Gateway Denial of Service Vulnerability
In Cisco Security Advisory
Beware: Identity Thieves Harvest Social Networks
Social networks are ripe for identity theft, with personal information easily up for grabs, security firm warns.
TJX Pays States for Cost of Investigating its Data Breach
The retail chain has reached a $9.75 million settlement with 41 states that helped untangle a major security leak.
Security Experts Visualize Botnets With an Eye Toward Defense
Not all botnets are organized in the same way. Understanding botnet design helps fight them more effectively.
Can an Enterprise iPhone Really Be Secure?
Analysis: As part of the evaluation process for any enterprise business solution, a risk analysis should be conducted beforehand.
Taking Pride in Nefarious Net Activities
Analysis: Thanks to Pretty Good Privacy encryption creator Phil Zimmermann for software that undermines suppression — and for keeping me out of jail.
Fake Online Harry Potter Movies Launch Malware Attack
Plus: A new password-stealing Trojan to guard against.
FTC Suspends Heavy Penalty Against Scareware Defendants
The FTC has suspended the majority of a fine levied against two defendants accused of selling bogus security software to up to a million consumers.
Security Essentials Does Its Job With No Frills
Microsoft Security Essentials may be the right tool for smaller businesses.
Don’t Get Tricked by Fake Microsoft Update E-Mails
I’ve received several phishing e-mails that look surprisingly authentic and professional.
Is It Time to Ditch the Antivirus?
To the average IT security practitioner, the idea of disabling antivirus on new machines might seem blasphemous.
Yet Another Malware Attack Spreads via Twitter
A link on Guy Kawasaki’s Twitter page purported to direct his followers to a porn video, but really, it was a virus attack.
Microsoft Security Essentials: The First Test Results Are In
Early test results show that Microsoft Security Essentials holds its own in malware detection and cleanup.
Securely Wipe Your Hard Drive
Reader Jim Bradley seeks a way to securely wipe the data from his hard drive. He writes:
EC Proposes Creation of Centralized Security Data Agency
EU took a step toward creating a pan-European IT system for security and surveillance Wednesday.
Adobe Issues Security Update for Shockwave Player
Adobe Systems released a patch on Tuesday for its Shockwave Player to fix a critical vulnerability.
Edition 1.1 Googled Security Events Corner
Google NEWS Search
Military Command Is Created for Cyber Security
Wall Street Journal – Siobhan Gorman, Yochi Dreazen – 22 hours ago
Maren Leed, a cyber-security expert at the Center for Strategic and International Studies, said the military’s closed computer networks could make it easier …
Gates Creates Cyber-Defense Command Washington Post
Its Official! Pentagon Cyber Command Gets Ready to “Stand Up” Huffington Post
Experts Converge at National Press Club on Cyber & Economic Security
MarketWatch – Jun 23, 2009
What: “Bridging the Gaps in our Nation’s Cyber Security: Connecting Leadership, Innovation, and Policy.” Panel Discussion in NPC Ballroom. …
Antivirus testing outfit: Microsoft Security Essentials makes the …
Computerworld – Gregg Keizer – 6 hours ago
Computerworld – Microsoft’s free security software passed a preliminary antivirus exam with flying colors, an independent testing company …
Microsoft to provide free anti-virus software Pak Watan
Md. poised to reap cyber security rewards
Baltimore Sun – Jun 23, 2009
(Baltimore Sun photo by Lloyd Fox / June 11, 2009) Maryland technology companies that specialize in cyber security are expecting to reap the benefit of …
Cyber security companies in Maryland getting hot, not bothered Baltimore Sun
TJX settles cyber security suit
Home Textiles Today – Jun 23, 2009
The company will pay $2.5 million to establish a Data Security Fund states can use to advance data security and technology. It will pay $7.25 million to …
TJX to pay $9.75 million for data breach investigations SearchSecurity.com
US: TJX agrees to pay $9.75m to settle security breach just-style.com
Cyber security tsar announced
Telegraph.co.uk – Duncan Gardham – 16 hours ago
A cyber security tsar is to be introduced in Britain to combat foreign countries, terrorists and criminals attempting to hack into government and business …
Tom Davis says he doesn’t want cyber-coordinator job FCW.com
Cyber Commander’s Dual-Hat Job GovInfoSecurity.com
Anger over ‘cyber security leaks’
BBC News – 9 hours ago
The Conservatives have urged ministers to make a statement on cyber security threats after reports about government plans appeared in several newspapers. …
Tory anger over cyber security leaks Public Service
Hospital confirms Jobs’ transplant
Philadelphia Inquirer – 15 hours ago
Keith Alexander, director of the National Security Agency. The creation of the command is part of an effort by the Obama administration to improve the …
NERC and Electric Industry Continue Efforts to Address Cyber Risk
Transmission and Distribution World – 7 hours ago
Initially launched by NERC President and CEO Rick Sergel in July 2008, the organization’s efforts to improve its response to cyber security have included …
Walker Joins NERC As Chief Financial And Administrative Officer North American Windpower
Will digital dissent win in Iran and China?
Christian Science Monitor – 3 hours ago
Their rulers are especially worried about their own security forces or top supporters turning against them in a fit of conscience or self-preservation if …
Web protest planned as Chinese government introduces Green Dam … New York Daily News
Internet boycott calls to mark China filter debut Reuters
Google Blog Search
Gordon Brown to appoint Britain’s first cyber security chief
6 hours ago by Ani
LONDON – The British Prime Minister is set to announce the appointment of the nation’s first cyber security chief who will be responsible to protect the country from terrorist computer hackers and electronic espionage. … June 5th, 2009 NEW DELHI – With information technology (IT) experiencing constant change, security systems connected with it should be revamped regularly, to ensure India is secured from external threats, experts have said. …
Simple Thoughts – Java and Web Blog – http://blog.taragana.com/
[ More results from Simple Thoughts – Java and Web Blog ]
The announcement on the Cyber Security Strategy looks like being …
7 hours ago by Toby
According to the Independent this morning, the announcement of the new Cyber Security Strategy that was promised last week and that I have been calling for over the weeks (years?) will take place tomorrow. … But the US-CCU’s findings show that other types of cyber-attacks are potentially much more destructive. Especially worrisome are the cyber-attacks that would hijack systems with false information in order to discredit the systems or do lasting physical damage. …
Lord Toby Harris – http://www.lordtobyharris.org.uk/
Concurring Opinions » On the Rumored Cyber Security Czar Candidate …
23 hours ago by Danielle Citron
According to Time magazine, fomer Congressman Tom Davis has emerged as a front runner for the newly created Cyber Security Czar position. The Time piece cited Davis’s authorship of the Federal Information Security Management Act of 2002 …
Concurring Opinions – http://www.concurringopinions.com/
TechSheep » Blog Archive » Military Command Is Created for Cyber …
20 hours ago
… Created for Cyber Security — WASHINGTON — Defense Secretary Robert Gates created a new military command dedicated to cyber security on Tuesday, reflecting the Obama administration’s plans to centralize and elevate computer security …
TechSheep – http://techsheep.com/
All Our Might » Blog Archive » Cyber security proposals
23 Jun 2009 by Jim Arkedis
Our banking system, our telephone communications and our electricity grid are all owned and run by private companies and are interconnected to the global computer network. We must anticipate that an adversary determined to cause economic damage or … Such an information clearinghouse could, without attribution, share information with other private entities so that everyone benefits. The timeliness of Wilson’s piece fits nicely with PPI’s cyber security event on Thursday. …
All Our Might – http://www.allourmight.com/
Homeland Security Earmarks – Jamie Dupree on wsbradio.com
17 hours ago
NPPD Infrastructure Protection and Information Security Multi-State Information Sharing and Analysis Center (MSISAC), NY, Office of State Cyber Security & Critical Infrastructure Coordination $3000000 Lowey; Clarke …
Jamie Dupree – http://wsbradio.com/blogs/jamie_dupree/
BBC NEWS | UK Politics | Anger over ‘cyber security leaks’ « euraktiva
9 hours ago by euraktiva786
BBC NEWS | UK Politics | Anger over ‘cyber security leaks’. The Conservatives have urged ministers to make a statement on cyber security threats after reports about government plans appeared in several newspapers. Tory home affairs spokesman Crispin Blunt … Obama a Very Smooth Liar   : Information Clearing House – ICH « euraktiva. Read and post comments | Send to a friend. Gordon Brown puts Israel lobbyist in charge of Britain’s Middle East policy – 12.160Mhz « eurak …
euraktiva – http://euraktiva786.wordpress.com/
New Mexico Independent » Heather Wilson warns about cyber security …
23 Jun 2009 by Gwyneth Doland
Last year’s advance of Russian tanks into Georgia was accompanied by the disruption of Georgian government computer systems. These are only public manifestations of a new reality: Attacks on computer systems will be an integral … Instead, she suggests strengthening our intelligence gathering in the area of cyber security, and proposes establishing a “safe harbor” where businesses and government can share information about cyber threats and how to defend against them. …
New Mexico Independent » Blog – http://newmexicoindependent.com/ – References
iKeepSafe Coalition: Promoting Cyber Safety, Security, and Ethics …
2 hours ago by Internet Keep Safe Coalition
Within a year of convening its first meeting, the group will submit a report to Congress and the Assistant Secretary for Communications and Information of its findings and make recommendations on how to increase online safety measures. … Inc. Christopher Bubb, AOL; Bradon Cox, NetChoice Coalition; Caroline Curtin, Microsoft; Brian Cute, Afilias U.S.A.; Jeremy Geigle, Arizona Family Council; Michael Kaiser, National Cyber Security Alliance; Christopher Kelly, Facebook …
iKeepSafe Coalition: Promoting Cyber Safety,… – http://ikeepsafe.blogspot.com/
Anger over ‘cyber security leaks’ | Polityczny Blog
10 hours ago
The Conservatives calls for ministers make a Commons statement on cyber security plans after reports appear in the media.
Polityczny Blog – http://www.polityka.sebaa.az.pl/
— Aurora Report says these are the results from today’s Google searches for “cyber security” | cyber security | information security | computer security
Around The Horn vol.1,127
China not backing off despite filter code post on Wikileaks
By jacqui@arstechnica.com (Jacqui Cheng) on security
China is filtering out criticism and diving in headfirst with its plan to roll out controversial filtering software on all PCs sold in China. The Chinese media quoted an unnamed source inside the Ministry of Industry and Information Technology, saying that the software will still come with all computers as of July 1 despite the discovery of massive security holes and vulnerabilities by security researchers.
News came out about China’s plan to implement Internet access control software, called the “Green Dam Youth Escort” earlier this month. The Windows-only software provides a mix of features, including whitelists, blacklists, and on-the-fly content-based filtering. The blacklists can be updated remotely, however, making Green Dam quite an attractive option for a government that likes to keep tight control over what kind of content its citizens are exposed to.
Microsoft Security Essentials beta available (Updated)
By emil.protalinski@arstechnica.com (Emil Protalinski) on Microsoft Security Essentials
Microsoft today released the Microsoft Security Essentials (MSE) beta on microsoft.com/security_essentials (redirects to Microsoft Connect which requires a Windows Live ID). The signing up process for the beta includes a seven-question survey. MSE is the company’s free, real-time consumer antimalware solution for fighting viruses, spyware, rootkits, and trojans. The beta is available in English and Brazilian Portuguese for the first 75,000 users, although Microsoft says this is a target number, and it is willing to increase it if necessary. The build number is 1.0.1407.00 (lower than the 1.0.2140.0 leaked build) and it comes in three flavors: for Windows XP 32-bit (7.51MB), for Windows Vista/7 32-bit (4.73MB), and for Windows Vista/7 64-bit (3.73MB). Before downloading, make sure your system satisfies the system requirements:
Microsoft Security Essentials not quite a must-have
By Seth Rosenblatt
Microsoft on Tuesday released its latest foray into security software as a limited beta. Microsoft Security Essentials, known in development as Morro, is limited to 75,000 downloads in four countries: the United States, Israel, Brazil, and China.
Security Essentials contains all the basic features that users have come to …
Q&A: Mark Abene, from ‘Phiber Optik’ to security guru
By Elinor Mills
Mark Abene first started using computers when he was about 9 years old, and by 12 he was exploring the electronic frontier from his home in Queens, New York. On bulletin board systems he swapped information with other phone phreakers and hackers, who formed the “Masters of Deception” group and …
Expedited airport-security service shuts down
By Matt Asay
Despite pulling in 260,000 travelers at $199 each, Clear’s expedited security-clearance program in 18 airports has shut down.
Verified Identity Pass, which operates the Clear service, said via e-mail and on its Web site that it was “unable to negotiate an agreement with its senior creditor to continue …
Originally posted at The Open Road
Twitter Trends Lead to Rogue AV
By Rik Ferguson on web
The misuse of Twitter trending topics (the most talked about subjects on Twitter) continues to gather pace. Following a post yesterday on social media guide Mashable, explaining how criminals were selectively posting to popular discussion topics to include links to malicious software, I saw criminals taking advantage of people talking about malware in order to push yet […]
Twitter Hack Spreads Porn Trojan
By Darknet on web-application-security
I had a spam tweet appear in my stream a while back and like Guy Kawasaki I also had absolutely no idea where it came from. Perhaps some kinda XSS flaw in Twitter when I visited a site that spawned the message (in a hidden iframe perhaps). It wouldn’t be the first time Twitter was having security […]
Slowloris – HTTP DoS Tool in PERL
By Darknet on web-security
This tool has been hitting the news, including some mentions in the SANS ISC Diary. It’s not actually a new attack (it’s been around since 2005) but this is the first time a packaged tool has been released for the attack. Slowloris holds connections open by sending partial HTTP requests. It continues to send subsequent headers at […]
Security Poised To Grab Bigger Piece Of IT Pie, Gartner Says
Analyst firm Gartner predicts security spending will comprise a larger percentage of overall IT budgets
CISO’s Fear Internal Data Threat
In Virus and Spyware
Most CISOs are most worried about insder threats to their data, not external attacks or those backed by foreign governments, according to a new report.
Microsoft and the Power of Free
In Virus and Spyware
Microsoft’s move to launch its’ new Morro endpoint AV beta as freeware could have a significant impact on the overall state of PC security, especially among consumers.
Tom Davis says he doesn’t want cyber-coordinator job
Tom Davis, the former congressman from Virginia who has been reported to be a top contender to be Obama’s cybersecurity coordinator, says he isn’t currently seeking the job. But, he also said “you never say never.”
Pentagon needs to take closer look at social networking, Gates says
The Defense Department wants to be linked in to the world, but must be wary of compromising operational security.
Open government Initiative may increase security woes
The Obama administration’s Open Government Initiative to make government information more accessible could lead to the inadvertent exposure of sensitive data.
Green Dam Deadline Remains Unchanged Despite U.S. Objections
Chinese authorities claim that its Green Dam censorware on all new PCs sold in the country is necessary to limit young people’s exposure to “harmful information.”
Green Dam Deadline Remains Unchanged Despite U.S. Objections
Chinese authorities claim that putting Green Dam censorware on all new PCs sold in the country is necessary to limit young people’s exposure to “harmful information.”
Cloudmark Goes After SMS Exploits
The carrier-grade mobile messaging security system provides content filtering, reputation data, and monitoring of text and multimedia messages.
Microsoft Security Essentials Beta Now Available
Known as “Morro,” Microsoft Security Essentials is the anti-malware component of Microsoft’s subscription security service, Windows Live OneCare.
ConSentry Impresses In Second Go-Round
Smart switch line enforces policy at the port.
ConSentry Impresses In Second Go-Round
Smart switch line enforces policy at the port.
Inside China’s Spam Crisis
Approximately 70% of all domains used in spam since the beginning of 2009 have a Chinese top-level domain.
Rollout: Egress Offers Rights Management As A Service
Switch encrypts data, restricts access, but only in Windows environments.
U.S. State Dept. Condemns China’s Green Dam Filter As Boycott Brews
China is insisting that computer makers install Web-filtering software known as Green Dam on all PCs sold in the country after July 1.
The Biggest Threat? It May Be You
When it comes to virtual server security, you might just be the weak link. Or, more precisely, your lack of planning, maintenance, and governance of that VM server farm.
Database Servers: Candy For Hackers
Sensitive information and poor security administration make tempting targets.
Practical Analysis: Follow The Feds’ Lead In Identity Management
Harnessing the power of a solid identity management system can substantially improve your company’s risk management posture.
Google Tries Blocking Pornography In China
The engineering effort may require disentangling Google.cn from search indexes associated with other Google search sites, like Google.com.
Google’s Anti-Malvertising.com Fights Off Bad Ads
The site was created because Google has a significant interest in making sure that ad blocking doesn’t become a standard security practice.
Microsoft Security Essentials Beta Coming Tuesday
Previously code-named “Morro,” the free software will replace Windows Live OneCare, which included both security and utility services for $49.95 per year.
Apple iPhone, iPod Security Flaws Get 45 Patches
Software patches were bundled with Apple’s iPhone 3.0 operating system released Wednesday.
iPhone Gets Enterprise IT Boost From Startup Apperian
Apple’s lack of interest in being a major player in enterprise IT has opened the door for Apperian to work with large corporations to develop applications for the iPhone.
China Making Green Dam Internet Filter Optional
The government’s edict prompted widespread derision from Chinese bloggers, objections from Chinese academics and lawyers, and criticism from security experts.
Former Google Employees Launch Web Malware Startup
The company will address changing malware distribution patterns and to provide a way to respond to Web security threats using automated techniques.
Apple Fixes Java Security Hole
The flaw could have allowed a Java applet to execute malicious code on affected Macs, potentially leading to information theft or a compromised system.
Twitter Security Heating Up In July
In an effort to raise awareness of browser security flaws, one researcher wants to post a vulnerability every day that shows the soft underside of the Fail Whale.
China’s Green Dam Software May Pose Legal Risk To U.S. Computer Makers
A research report indicates that the Web-filtering software mandated by the Chinese government contains unauthorized, proprietary code from a Green Dam competitor.
Lawmaker: Power Grid Vulnerable To Cyberattack
Hackers could bring down electrical grids serving entire regions of the U.S., leaving homes and businesses dark for months, Congressman says.
China ‘Green Dam’ Censorware Called Security Risk
Chinese authorities claim the software is necessary to protect people from pornography, but the software has been found to block politically sensitive terms.
U.S. Court Weighs E-mail Privacy, Again
At issue: whether e-mail messages deserve the same privacy protection as telephone calls.
Army Unblocks Some Social Media Sites
U.S. troops within the contiguous United States can now access Facebook, Delicious, Flickr, Twitter, Vimeo, and Web-based e-mail. YouTube and some other sites are still blocked.
Mac Users Warned Of Porn Malware Threat
Trojan software presents visitors to certain porn sites with a pop-up message to download a Video ActiveX Object; the download carries Mac malware.
China’s Internet Filtering Plan Widely Criticized
Critics claim “Green Dam Youth Escort” Internet filtering software for PCs violates licensing agreements and anti-monopoly laws.
Microsoft To Launch Morro Antivirus ‘Soon’
The free offering will replace subscription Windows Live OneCare service.
Rollout: How Much Is Bot Detection Worth To You?
Damballa’s appliance shows promise, but it still has a lot of ground to cover.
Insider Snooping Becoming More Common
In a survey, most respondents acknowledged being able to circumvent security access controls at their workplace.
Symantec, McAfee In Settlement Over Subscriptions
Both companies will pay $375,000 in penalties and costs and will now make detailed disclosures to consumers.
Microsoft Fixes Record Number Of Vulnerabilities
The company’s June Patch Day included 10 security bulletins to fix 31 threats in Microsoft products.
Is Apple’s iPhone 3GS Enterprise Ready?
The 3.0 software and iPhone 3GS offer incremental improvements for corporate deployments, but experts note some key elements are still missing.
Black Hat Founder Tapped To Advise Homeland Security
The fact that a former hacker will be palling around with other HSAC members shows that the government is casting a wide net for perspectives on cybersecurity.
Alleged T-Mobile Data Offered To Highest Bidder
A note offering the data for sale says that the company’s databases, confidential documents, and financial documents were stolen.
China To Require Filtering Software On PCs
Starting July 1, PC makers will have to install pornography-blocking app Green Dam Youth Escort on all computers sold in China.
Air Force Names Cyberwarfare Commander
The 24th Air Force, which will likely be based at Lackland Air Force Base in Texas, will focus exclusively on cyberwarfare as part of the larger Air Force Space Command.
FTC Shuts Down ‘Worst ISP In U.S.’
Pricewert LLC is accused of hosting and actively distributing child pornography, malware, and spam.
Federal CIO Kundra Looks Forward To Data.Gov 2.0
The upgrades to the site, which will be available in a few months, will feature new ways to find and use data, including the ability to tag data sets.
Google Widens Its Gaze In Street View
Google’s continuous corridor of 3-D space with building facades and roadway geometry is generated virtually using laser landscape measurements and picture difference comparisons.
Verizon Business Unveils ‘Computing As A Service’
The company’s CaaS users will be able to access a real-time self-service portal to manage physical and virtual servers, network devices, storage, and backup services.
RIM Issues Patch For BlackBerry Vulnerability
Enterprise BlackBerry smartphone users could be at risk if they open a maliciously crafted PDF, Research In Motion says.
Homeland Security Keeping Central Cybersecurity Role
The department’s operational responsibility won’t be undercut by the cybersecurity coordinator, a DHS undersecretary nominee says.
Government Accidently Posts Sensitive Nuclear Documents Online
The 267-page document contains addresses and descriptions of civilian nuclear sites around the country.
Homeland Security Names New Cybersecurity Officials
Philip Reitinger, who worked in cybersecurity for Microsoft and fought cybercrime for the Department of Justice, will help to coordinate cybersecurity efforts across the government.
Mobile Phones Face Hacking Threat, Experts Say
A flaw — which enables criminals to access a cellphone data connection, steal data or install or remove programs — gained wider attention at the BlackHat Europe security conference.
Rolling Review Wrap-Up: Smartphone Security
Each product we looked at showed different core strengths. Know your environment to find the best tool for your mobile device fleet.
Google Executive To Become Federal Deputy CTO
Andrew McLaughlin will find that he isn’t the only ex-Google employee serving the Obama administration.
Cybersecurity Review Finds U.S. Networks ‘Not Secure’
The report dovetails with President Obama’s call for the creation of a cybersecurity coordinator who will orchestrate and integrate federal cybersecurity policies and agendas.
Obama Announces White House Cybersecurity Position
Names that have been bandied about include acting White House cybersecurity chief Melissa Hathaway and Microsoft VP Scott Charney.
Microsoft Warns Of ‘Browse-And-Get-Owned’ DirectX Flaw
The flaw could allow a remote attacker to execute malicious code by convincing or duping a user to open a specially crafted QuickTime media file.
Government Wrestles With Social Media Records Retention Policies
The National Archives is trying to navigate complex regulations that require capturing and storing all sorts of content in the age of social media, cloud computing, and seemingly endless storage.
White House Launching Transparency Blog
In a nod to openness and citizen participation in government, the Obama administration also will open White House blogs to public comments.
Obama Should Scrap Cybersecurity Czar, Analyst Says
Gartner expert says president’s plan to protect nation’s computing infrastructure won’t work.
Sex the Bait in Mass Orkut Compromise
By Rahul Mohandas on Web and Internet Safety
With the advent of Web 2.0, social networking websites have become an easy target for online fraud and other identity scams. Lately, we have seen Twitter being used to phish out personal information, as well as MySpace scams and Facebook spams. With more than 15 percent of the traffic from India, Orkut is perhaps the most […]
More Password Theft Shenanigans
By Karthik Raman on Malware Research
Recently, Pedro Bueno wrote about “dumb” malware authors hardcoding their login credentials into their password stealing trojan. The malware he referenced, PWS-Banker.gen.i, ostensibly came from Brazil. Today, we found the same negligence in a similar piece of Chinese malware detected as PWS-Banker.gen.de. When run, the password stealer trojan queries for the infected host’s IP address using three web-based IP address lookup […]
Symantec unveils endpoint protection services
Symantec now offers managed endpoint protection services for round-the-clock monitoring and management of computers that use Symantec security products.
Spammer Ralsky pleads guilty to stock fraud
Alan Ralsky, a spam kingpin who was convicted of felony bank fraud in 1995, could face more than seven years in prison after pleading guilty in a stock fraud case involving spam messages that pumped up Chinese “penny” stocks.
China stands by Web filter program despite protests
China’s deadline for the installation of Web filtering software on new PCs hasn’t changed, it said Tuesday, despite growing protests from the U.S. government and Chinese Internet users.
Can you manage an iPhone like a BlackBerry?
Users love the iPhone, but IT does not. The biggest complaints: The iPhone can’t be managed for security and access policies like a BlackBerry can. Businesses can buy a BlackBerry Enterprise Server or Motorola Good for Enterprise server to manage user profiles over the air, ensuring that users conform to password policies, encryption policies, app-installation restrictions, and so on, as well as have their e-mail, VPN, and other settings preconfigured to reduce hands-on deployment effort.
Microsoft caps free security software downloads
Microsoft will limit the number of downloads for the beta of Windows Security Essentials, its new free antivirus software, when it posts the program later today.
Free security product vets Twitter links
As Twitter becomes increasingly abused by hackers, Finjan Software released on Tuesday a free browser add-on with a new feature that scans links and warns if they point to a page containing malware.
McAfee expands in China for expected security boom
McAfee is expanding its staff in China amid a boom in the country’s security market fueled by the launch of next-generation mobile networks.
IBM to manage Qwest services
Qwest and IBM announced last week that the two companies had signed a five-year agreement for IBM to manage Qwest services targeted to Qwest’s midsize business customers including unified communications, managed security and network management.
Trustive Wi-Fi hotspots get VPN shield
Wireless aggregator Trustive claims has come up with a way for its customers to secure their Internet access even while using public Wi-Fi hotspots lacking such security.
Google fixes ‘critical’ security hole in Chrome
Google has plugged a security vulnerability in its Chrome browser that the company considers critical.
Titsup TSA partner closes airport express lanes
You are not in the Clear
America’s airport security checkpoints just lost some express lanes.…
Shutters brought down on mortgage foreclosure racket
Sub-prime scam
A bogus mortgage foreclosure prevention operation that traded in misery has been shut down by a US court.…
Microsoft begins Security Essentials downloads
To Morro comes today
Microsoft has begun offering limited trial downloads of its no-added-cost anti-malware tool, targeted at consumer desktops.…
DHS killing satellite self-spying program
Space cops ‘not an urgent issue’
America is reportedly abandoning its plans to use satellites to spy on itself.…
Nine-ball attack splits security researchers
Ruck over whether figures stack up
Security researchers are split over the seriousness of a web attack dubbed “Nine-ball” which broke onto the internet last week.…
Social networking big boys must bow to EU data laws
The Fat Data Controllers
Social networking sites are legally responsible for their users’ privacy, Europe’s privacy watchdogs have confirmed. A committee of data protection regulators has said that the sites are ‘data controllers’, with all the legal obligations that brings.…
Notorious spammer Ralsky pleads guilty to stock scam
Father and son-in-law spammers face slammer
Notorious spammer Alan Ralsky faces up to 87 months’ imprisonment after pleading guilty to participation in a pump-and-dump stock spam scam.…
Manchester council caned over school data breach
Must do better
Manchester City Council has been rapped over the knuckles for the loss of two laptops containing sensitive personal information on teachers and workers at local schools.…
US city ends FaceSpaceGooHoo log-in grab
Bozeman bows
After a virtual avalanche of news coverage, the City of Bozeman, Montana has decided it will no longer ask job applicants for their FaceSpaceGooHoo log-ins.…
New Thunderbird out, patches couple of vulnerabilities, (Tue, Jun 23rd)
Couple of readers wrote in to say that a new version of Thunderbird has been released. Version 2 …(more)…
Help us: How to make ISC/DShield more useful, (Tue, Jun 23rd)
I am looking for feedback for the next iteration of the ISC/DShield web site. What kind of informati …(more)…
Slowloris and Iranian DDoS attacks, (Tue, Jun 23rd)
In last couple of days we posted two diaries (http://isc.sans …(more)…
Nevada Law Requires PCI DSS Compliance (June 20, 2009)
As of January 1, 2010, companies doing business in the state of Nevada that accept payment cards must be compliant with the Payment Card Industry Data Security Standard (PCI DSS)…….
Proposed Law Would Give Canadian Law Enforcement and National Security Agencies Easy Access to ISP Subscriber Information (June 18, 2009)
Proposed legislation in Canada would allow police and national security agents “timely access” to information including names, street addresses and IP addresses of Canadian Internet service provider (ISP) subscribers…….
Criminalization of Hacking Software in Germany Withstands Test of Constitutionality (June 20, 2009)
The German Federal Constitutional Court has ruled as inadmissible an appeal that challenged the constitutionality of legislation criminalizing the use of hacking software…….
Heartland CEO Moving Forward With an Eye to Improving Industry Security (June 17 & 22, 2009)
Analysts have been favorably impressed by Heartland Payment Systems Inc…….
Bozeman Backs Down on Demand for Job Applicants’ Social Networking Site Logins (June 18 & 19, 2009)
Facing criticism from citizens and unwanted media coverage, the city of Bozeman, Montana has called off its practice of asking job applicants to provide usernames and login information for any social networking sites they use regularly…….
Spam Spreading ZBot Masquerades as Outlook Update (June 22, 2009)
Spam masquerading as a Microsoft Outlook security and stability update actually infects computers with ZBot, a Trojan horse program that steals sensitive information…….
RSPlug Trojan Variant Targets Macs (June 22, 2009)
A Trojan horse program that infects Mac users has been detected on legitimate game download sites…….
Just Half of Small Businesses Backup Daily (June 21, 2009)
According to a survey of 945 IT managers at companies in Hong Kong, Singapore and Australia, 36 percent of respondents said they believed data loss had a significant effect on their business, but just seven percent of the respondents rated the impact of data loss as “high…….
ICANN Committee Calls for End to DNS Redirections (June 10 & 22, 2009)
A report from the Security and Stability Advisory Committee (SSAC) of the Internet Corporation for Assigned Names and Numbers (ICANN) says that DNS redirections present risk of “erosion of trust relationships (and) the creation of new opportunities for malicious attack…….
US Formally Opposes China’s Demand For Pre-Installed Filtering Software on PCs (June 22 & 29, 2009)
The US government has officially opposed China’s mandate that filtering software be installed on all PCs sold in or shipped to that country…….
Cybersecurity czar candidate questions clout of new position
By Robert Westervelt
Former U.S. Congressman Tom Davis, a leading candidate for the White House cybersecurity czar, says the job has a number of major challenges to overcome.
Symantec offers endpoint protection management, monitoring services
By Neil Roiter
Symantec responds to pain points of managing endpoint protection with two managed services to help deploy and maintain antivirus, NAC products and endpoint security suites.
Symantec Puts Endpoint Security on Managed Services Menu
Symantec adds a new batch of managed security services for protecting enterprise endpoints. According to Symantec, the goal of Symantec Managed Endpoint Protection Services is to help companies dealing with staff shortages to better meet their security needs.
– Symantec unveiled a new set of managed services June 23 as part of a push around enterprise security. Symantec Managed Endpoint Protection Services features around-the-clock performance monitoring for Symantec’s enterprise security software SEP (Symantec Endpoint Protection), SNAC (Symantec Ne…
Notorious Spammer Faces Federal Prison
A Michigan man in charge of a large spam operation has pleaded guilty to fraud and money laundering charges. According to federal prosecutors, spammer Alan Ralsky was in charge of an international spam operation that tried to manipulate stock prices.
– A Michiganman called quot;the world’s most notorious illegal spammer quot; by a federal prosecutor has pleaded guilty to fraud and money laundering charges. As part of his plea, Alan M. Ralsky, 64, of West Bloomfield, Mich., admitted to overseeing a spam operation that sought to manipulate …
Accused Spam King Alan Ralsky Pleads Guilty
In Cyber Justice
Alan Ralsky, a 64-year-old Michigan man that federal investigators say was among the world’s top spam kingpins, pleaded guilty on Monday to running a multi-million dollar international stock fraud scam powered by junk e-mail. Ralsky (pictured at right, courtesy of Spamhaus) and his son-in-law and chief financial officer Scott K. Bradley, 38, also of Michigan, pleaded guilty to conspiracy to commit wire fraud, money laundering and to violate the CAN-SPAM Act. Under the terms of his plea agreement, Ralsky faces as much as 87 months in prison and a $1 million fine, while Bradley could get as much as 78 months in prison and a $1 million fine under the federal sentencing guidelines. The Ralsky plea caps a long effort by the government to nab one of the most prolific spammers. In September 2005, the FBI raided Ralsky’s home, but it wasn’t until early 2008 that the government indicted Ralsky
Brief: Firms atwitter over social-net threats
Firms atwitter over social-net threats
Brief: Microsoft’s launches free AV offering
Microsoft’s launches free AV offering
Free .pdf Issue of BSD Magazine Available
By Richard Bejtlich
Karolina at BSD Magazine wanted me to let you know that she has posted a free .pdf issue online. I mentioned this issue last year and its focus is OpenBSD. Check it out, along with Hakin9!
Richard Bejtlich is teaching new classes in Las Vegas in 2009. Regular Las Vegas registration ends 1 July.
Copyright 2003-2009 Richard Bejtlich and TaoSecurity (taosecurity.blogspot.com and www.taosecurity.com)
The Problem with Automated Defenses
By Richard Bejtlich
Automation is often cited as a way to “do more with less.” The theory is that if you can automate aspects of security, then you can free resources. This is true up to a point. The problem with automation is this:
Automated defenses are the easiest for an intruder to penetrate, because the intruder can repeatedly and reliably test attacks until he determines they will be successfully and potentially undetectable.
I hope no one is shocked by this. In a previous life I worked in a lab that tested intrusion detection products. Our tests were successful when an attack passed by the detection system with as little fuss as possible.
That’s not just an indictment of “IDS”; that approach works for any defensive technology you can buy or deploy off-the-shelf, from anti-malware to host IPS to anything that impedes an intruder’s progress. Customization and localization helps make automation more effective, but that tends to cost resources. So, automation by itself isn’t bad, but mass-produced automation can provide a false sense of security to a certain point.
In tight economic conditions there is a strong managerial preference for the so-called self-defending network, which ends up being a self-defeating network for the reason in bold.
A truly mature incident detection and response operation exists because the enterprise is operating a defensible network architecture, and someone has to detect and respond to the failures that happen because prevention eventually fails. CIRTs are ultimately exception handlers that deal with everything that falls through the cracks. The problem happens when the cracks are the size of the Grand Canyon, so the CIRT deals with intrusions that should have been stopped by good IT and security practices.
Richard Bejtlich is teaching new classes in Las Vegas in 2009. Regular Las Vegas registration ends 1 July.
Copyright 2003-2009 Richard Bejtlich and TaoSecurity (taosecurity.blogspot.com and www.taosecurity.com)
You Know You’re Important When…
By Richard Bejtlich
You know you’re an important when someone announces a “Month of Bugs” project for you. July will be the Month of Twitter Bugs, brought to my attention in this story by Robert Westervelt. The current project is led by a participant in the Month of Browser Bugs from three years ago named Avi Raff.
I don’t see projects like that as being irresponsible. What would be more irresponsible is selling the vulnerabilities to the underground. Would the critics prefer that? In many cases, “Month of” projects are the result of running into resistance from developers or managers are not taking vulnerabilities seriously. In many cases the vulnerabilities are already being exploited. Sure, packaging all of the vulnerabilities into a “Month of” project gains attention, but isn’t that the point?
Richard Bejtlich is teaching new classes in Las Vegas in 2009. Regular Las Vegas registration ends 1 July.
Copyright 2003-2009 Richard Bejtlich and TaoSecurity (taosecurity.blogspot.com and www.taosecurity.com)
US creates military command for cyber battlefield (AFP)
In us
AFP – The US military announced a new “cyber command” designed to wage digital warfare and to bolster defenses against mounting threats to its computer networks.
First Look: Microsoft Security Essentials (PC World)
In technology
PC World – The beta version of Microsoft Security Essentials, a free program that fights viruses and spyware, is now available for download. The app, previously code-named Morro, replaces Windows Live OneCare and fights the usual rogues’ gallery of PC threats, including worms, Trojans, and other troublemakers.
Spotting the Antivirus Rogue (PC World)
In technology
PC World – Fake antivirus programs have become a favorite bad-guy scam for worming into your wallet, with a plethora of false reports of malware infections meant to to scare the unsuspecting into shelling out $50 for worthless software.
Is Microsoft’s ‘Morro’ Malware in Disguise? (PC World)
In technology
PC World – Goodbye Windows Defender, hello Windows Security Essentials.
Free Security Product Vets Twitter Links (PC World)
In technology
PC World – As Twitter becomes increasingly abused by hackers, Finjan Software released on Tuesday a free browser add-on with a new feature that scans links and warns if they point to a page containing malware.
Cisco Security Center: IntelliShield Cyber Risk Report
June 15-21, 2009
Report Highlight: Tougher EU Privacy Regulation for Social Networking Sites
AP Issues Strict Facebook, Twitter Guidelines to Staff
By David Kravets
The Associated Press tells its 4,000 employees and journalists to delete impartial comments, even those by others, from their personal Facebook accounts. The union representing AP reporters calls it the most stringent policy it has ever seen.
Cyber Security Czar Front-Runner No Friend of Privacy
By Ryan Singel
An examination of former Congressman Tom Davis’ record shows that he’s been on the wrong side of key privacy issues, including warrantless internet surveillance, and the controversial REAL ID Act, which aims to turn state driver’s licenses into a national identification card.
Nokia, Siemens Help Iran Spy on Internet Users
By Kim Zetter
Western tech companies sold Iran the “deep packet inspection” systems the government is now using to monitor dissent, The Wall Street Journal reports.
A Violent Virus Cure?
If you’re hard drive is infected by a virus, you don’t have to resort to truly drastic means to make sure it’s really clean. Learn more in this tip.
High Profile Twitter Hack Spreads Porn Trojan
A criminal is using entrepreneur Guy Kawasaki’s Twitter account to spread malware.
First Look: Microsoft Security Essentials
Here is what you need to know about Microsoft’s free security app, Microsoft Security Essentials.
Can Facebook Be Private?
Worried about privacy on Facebook? Here’s how to keep your personal information safe.
‘Enterprise Facebook’ Enjoys Major Adoption
Government consultancy Booz Allen Hamilton’s homegrown enterprise 2.0 portal is a roaring success.
Spotting the Antivirus Rogue
Check out a short guide from Sunbelt Software to help identity a favorite bad guy scam job.
Regulators: EU Data Protection Laws Apply to Social Networks
Social-networking sites, and in some instances their users, must keep the privacy of the people whose information they exchange on line.
Cloudmark Security Suite Addresses Growing SMS Spam
As mobile users are more frequently pestered by SMS spam, one security vendor is applying its experience with stopping e-mail spam for mobile networks.
Google Fixes ‘Critical’ Security Hole in Chrome
Google has identified a critical security hole in Chrome and fixed it in the latest release of the browser.
Is Microsoft’s “Morro” Malware in Disguise?
Windows Security Essentials, previously dubbed “Morro,” enters its public beta today. And contrary to earlier reports, the program doesn’t proxy all of your Web traffic through Microsoft’s servers: Go figure?
Proxy Servers Keeping Web Access in Iran
An unknown number of proxy servers set up in recent days are being used to help Iranians to maintain access to unfiltered Web content amid a crackdown.
Symantec Unveils Endpoint Protection Services
Symantec now offers managed endpoint protection services for round-the-clock monitoring and management of computers that use Symantec security products.
Microsoft Limits Free Security Software Downloads
Microsoft will limit the number of downloads for the beta of Windows Security Essentials, its new free antivirus software.
McAfee Expands in China for Expected Security Boom
McAfee is expanding its staff in China amid a boom in the country’s security market it expects to continue with the launch of next-generation mobile networks.
Free Security Product Vets Twitter Links
Finjan Software released on Tuesday a free add-on with a new feature that scans links, even if those links have been shortened.
Around The Horn vol.1,126
New Facebook blog: We can hack into your profile
By Caroline McCarthy
Well, here’s an innovative way to get some buzz: FBHive, a new blog devoted to the discussion of all things Facebook, has debuted with the revelation that its creators have discovered a hack that can expose some crucial profile data.
No, it won’t expose your personal photos or …
Originally posted at The Social
Q&A: Kevin Mitnick, from ham operator to fugitive to consultant
By Elinor Mills
There is no question who the most famous hacker is. One of the first computer hackers prosecuted, Kevin Mitnick was labeled a “computer terrorist” after leading the FBI on a three-year manhunt for breaking into computer networks and stealing software at Sun, Novell, …
Accusations of Murder, Jealousy, Revenge – Twitter Hacking
By Rik Ferguson on web
He probably only just woke up, but today is already a very bad day for American TV actor Dorion Standberry, one of the stars of College Hill on the BET network. His Twitter profile says “I act, I model, I sing, I socialize!!“, he can add “I get pwned” to that list now too. It appears that […]
IT Managers Under-Estimate Impact Of Data Loss
By Darknet on Information-Security
I find it a little surprising in this day and age that such a low percentage of IT managers believe data loss is a low impact issue. Don’t they read the news? Don’t they understand how losing customer trust can really effect your bottom-line? I would have thought 30% of respondents thinking data loss was high impact […]
Related Searches
on Ask.com
DNSSEC Showing More Signs Of Progress
The Domain Name System (DNS) security protocol is finally making inroads on the Internet infrastructure front, but big hurdles remain for widespread, smooth adoption
Facebook Hack Beats Privacy Settings
In Vulnerability Research
After waiting more than two weeks, bloggers went public June 22 with a report of a vulnerability on Facebook that can be exploited to reveal personal information. Facebook has reportedly fixed the flaw.
Cybersecurity, info sharing: House approves 2010 funding boost
The House recently approved a fiscal 2010 budget plan for the Justice Department that would increase funding compared to 2009 levels for some key information technology programs.
New organization to address interoperability between social media, ID management
The Kantara Initiative will provide a venue for the identity management industry to cooperate in developing interoperable technologies that will better enable identity-based applications and other interactive online transactions.
DOD: Be wary of social media’s ‘loose lips’
Two Defense Intelligence Agency experts explain how adversaries can use social-networking tools to gather information on targets.
ConSentry Impresses In Second Go-Round
Smart switch line enforces policy at the port.
Inside China’s Spam Crisis
Approximately 70% of all domains used in spam since the beginning of 2009 have a Chinese top-level domain.
Rollout: Egress Offers Rights Management As A Service
Switch encrypts data, restricts access, but only in Windows environments.
U.S. State Dept. Condemns China’s Green Dam Filter As Boycott Brews
China is insisting that computer makers install Web-filtering software known as Green Dam on all PCs sold in the country after July 1.
The Biggest Threat? It May Be You
When it comes to virtual server security, you might just be the weak link. Or, more precisely, your lack of planning, maintenance, and governance of that VM server farm.
Top European CIO’s book translated to English
One of the most popular books amongst European CIOs is now available in English. IT’s Hidden Face, written by Claude Roeltgen the CIO of one of Luxembourg’s top banks has been a top read amongst CEOs, CIOs and government ministers across the continent.
Related Searches
on Ask.com
ScanSafe labels Nine-Ball attack as ‘hype’
Security vendor Websense has been blasted for allegedly hyping up the so-called ‘Nine-Ball’ mass website compromise it made public earlier this week.
Related Searches
on Ask.com
Defense stalwarts see cash in cybersecurity
As the U.S. government goes on a cyberdefense spending spree, major government contractors are beefing up their network security expertise so they can get in on the action.
Working with consultants part 4
One test you can apply to judge the professionalism of a prospective consultant is to ask her to identify the limits of her professional competence. A professional consultant will clearly identify the limits of her knowledge.
AMD Chips Used in Iranian HPC for Rocket Research
The Web site of an Iranian research institute has posted the specifications of a high-performance computer that it built using AMD dual-core Opteron chips despite a U.S. trade embargo.
Related Searches
on Ask.com
Heartland Commended for Breach Response
Heartland Payment Systems CEO Robert Carr has made several moves to address security following the massive data breach at his payment processing company earlier this year.
Related Searches
on Ask.com
Fraudsters try to scam security expert on eBay
When security expert Bruce Schneier tried to sell a used laptop on eBay, he thought it would be easy. Instead, a sale was aborted twice — first by a scammer using a hacked eBay account and then by a buyer who tried to trick Schneier into sending her the laptop after she cancelled payment.
Related Searches
on Ask.com
Sensitive data made available on Parcelforce website
Sensitive personal data including names, addresses and postcodes has been made publicly available on Parcelforce’s website.
Related Searches
on Ask.com
Facebook tackles potent click fraud scam
Disgruntled advertisers turn anti-social
Facebook is investigating reports that advertisers on the social networking site have been left well out of pocket as a result of click fraud.…
Related Searches
on Ask.com
Iranian hacktivists hand-crank DDoS attack
Farsi hackers do without botnets
The controversial outcome of the Iranian elections has spawned a parallel conflict on the internet.…
Related Searches
on Ask.com
Scanning Windows Deeper With the Nmap Scanning Engine
Category: Penetration Testing
Paper Added: June 22, 2009
A Virtually Secure Browser
Category: Home & Small Office
Paper Added: June 22, 2009
phpMyAdmin Scans, (Sun, Jun 21st)
Happy Fathers Day (at least those in the USA), Earlier today one of our readers (Thanks Alice) noti …(more)…
Say it ain’t so…. , (Mon, Jun 22nd)
According to the Australian version of the SORBS website, Michelle (formerly Matthew) Sullivan …(more)…
Incident response planning
By Robert Westervelt
Jack Phillips, managing partner of security research firm, IANS, talks about how companies can prepare to appropriately handle a security incident.
Gartner sees better days ahead for security budgets
By Robert Westervelt
Investments in managed security services, intrusion prevention systems and multifunction firewalls help buoy IT security budgets.
Financial security pros expect improved funding in second half of 2009
By Marcia Savage
A SearchFinancialSecurity.com survey indicates a security spending rebound in financial services with companies investing in authentication, encryption and network access control.
Related Searches
on Ask.com
Security researchers develop browser-based darknet
By Robert Westervelt
Called Veiled, the darknet only requires participants to use an HTML 5-based browser to connect and share data anonymously.
Database monitoring, encryption vital in tight economy, Forrester says
By Erin Kelly
A new report from Forrester Research Inc. examines eight database and server data security technologies and recommends small steps that can make a big difference.
Related Searches
on Ask.com
Virtual appliances boost flexibility, improve security
By Eric Ogren
Companies see the benefits of placing network-oriented security on a faster processor.
Botnet platform helps cybercriminals bid for zombie PCs
By Robert Westervelt
Infected PCs are sold again and again on a new platform that enables cybercriminals to buy and sell victim’s machines.
Month of Twitter Bugs project to document Twitter flaws
By Robert Westervelt
Security researcher Aviv Raff will document a number of cross-site scripting (XSS) flaws and other errors threatening Twitter users.
Microsoft cracks down on click fraud ring
By Robert Westervelt
Fraudsters used a click farm to simulate hundreds of thousands of clicks for specific advertisements. Experts say click fraud threatens the online advertising industry.
IT pros find corporate firewall rules tough to navigate
By Eric Ogren
Tweaking rules could result in disrupting business communications or opening a hole for unauthorized traffic. Firewall management tools ease the burden.
Security Software Market Revenues Jump Worldwide
Gartner estimates the security software market increased 18.6 percent in 2008 to $13.5 billion worldwide, with Symantec, McAfee and Trend Micro leading the way. According to Gartner, some of the growth was due to increased demand for appliance-based products.
– The market for security software made a strong showing in 2008, jumping nearly 20 percent to $13.5 billion, according to Gartner. The figure represents a roughly $2 billion increase for the market over 2007. Of particular note was an increase in demand for appliance-based products within e…
Brief: Security-software market shrugs off economy
Security-software market shrugs off economy
Spammer Ralsky Pleads Guilty to Stock Fraud (PC World)
In technology
PC World – Alan Ralsky, a spam kingpin who was convicted of felony bank fraud in 1995, could face more than seven years in prison after pleading guilty in a stock fraud case involving spam messages that pumped up Chinese “penny” stocks.
SB09-173: Vulnerability Summary for the Week of June 15, 2009
Vulnerability Summary for the Week of June 15, 2009
Cisco Security Center: IntelliShield Cyber Risk Report
June 15-21, 2009
Report Highlight: Iran Election Aftermath Plays Out Online
Oh, You Vulnerable Twit! Why Twitter Needs Security
The phenomenon known as Twitter continues to grow at a rapid pace. Here’s why you need to beware of “twishing”—that would be Twitter phishing—and other Twitter security issues.
Google News “cyber security” | cyber security | information security | computer security
China Stands by Web Filter Program Despite Protests
PC World – Owen Fletcher – 4 hours ago
The US has asked China for a dialogue about the potential impact of the mandate on trade, effects on the free flow of information and “serious technical …
World Briefing | Asia China: Artist Urges Online Boycott New York Times
US envoy denies complaining about Web filter People’s Daily Online
China sticks to web filter plan The Press Association
Hollywood Reporter – NewsFactor Network
Information Security: The Good, The Bad and The Ugly
TMC Net – Kevin G. Coleman – 17 hours ago
Whether you call it information security, cyber security or cyber warfare makes no difference; the situation is the same! Information security is treated as …
arcelormittal security guard seeks charges against cop
Times – Ken Kosky – 5 hours ago
Karimi reported that the security officer approached in an aggressive manner and requested information about the traffic stop, Price said. …
Check out your Social Security wage statement
Examiner.com – 17 hours ago
Although a note with a return address of IRS is likely to strike fear in the most stalwart heart, an item from the Social Security Administration deserves …
Tips for how to boost your Social Security benefits Bradenton Herald
A way to boost Social Security Belleville News Democrat
Cyber Security Czar Front-Runner No Friend of Privacy
Wired News – Ryan Singel – 11 hours ago
But Davis could excel in a new role as cyber security czar, says Marc Rotenberg, who heads the Electronic Privacy Information Center. …
Private Facebook Info Exposed By Simple Hack
Dark Reading – Graham Cluley – 2 hours ago
Facebook’s security has been called into question after the creators of a new blog discovered a hack that can expose private profile information of any user …
Facebook flaw puts members at risk MyADSL
Cybersecurity To Push For Standard For Info Security Products
Bernama – Jun 19, 2009
KUALA LUMPUR, June 19 (Bernama) — CyberSecurity Malaysia, the country’s vanguard of cyber security, is pushing for the Common Criteria for information …
Securing critical infrastructure needs holistic approach, panel says GCN.com
Analysis: One Step Behind Nextgov
Trusted Computing Group to Demonstrate Pervasive Security at …
Business Wire (press release) – 19 hours ago
The Gartner Group Information Security Summit will be held Monday, June 29 – Wednesday, July 1. The Summit will be located at the Gaylord National Resort, …
Financial security pros expect improved funding in second half of 2009
SearchSecurity.com – Marcia Savage – 20 hours ago
After months of belt tightening during the global recession, some financial security …
Smart Grid Security Frenzy: Cyber War Games, Worms and Spies, Oh My!
Reuters – Katie Fehrenbacher – Jun 18, 2009
According to executives at computer security firm IOActive: Studies show that overall project costs are 60 times higher when gaps in information security …
Smart Meter Security: A Work in Progress Greentech Media
Google Blog Search “cyber security” | cyber security | information security | computer security
The Cyber Shot Twittered Around the World : Information Security …
11 hours ago by anthonymfreed@gmail.com (Information Security…
The Department of Homeland Security (DHS) Office of Cybersecurity and Communications (CS&C) National Cyber Security Division (NCSD), the Department of Defense (DoD) and National Institute for Standards and Technology (NIST) Information …
Information Security Resources – http://information-security-resources.com/
[ More results from Information Security Resources ]
Risk Management and Information Security: Merging into one …
19 hours ago by Laura Mather
Three times in the past two weeks I’ve been privy to a conversation about the difference between risk management and information security. Most organizations have separate functions for risk management and information security. …
Silver Tail Blog – http://silvertailsystems.wordpress.com/
Cyber security agency ties up with British firm
35 minutes ago by Ians
NEW DELHI – The government agency in charge of cyber security Tuesday signed an agreement with British IT and communication solutions provider BT for enhancing computer security and technology sharing. …. April 23rd, 2009 US adviser says cybersecurity must be joint effortSAN FRANCISCO — The challenge of protecting the government’s computer networks is too big for any one agency to handle alone, a top adviser to President Barack Obama said Wednesday. …
The Gaea News – http://blog.taragana.com/n/
Security Information and Event Management Software Market Defies …
2 hours ago by Security Management News
The vital importance of security software to organizations of all sizes has been clearly demonstrated by the news that worldwide security software market.
Exaprotect BlogManager – http://blogs.exaprotect.com/
Most companies don’t protect vital information adequately …
13 hours ago by Alan Harten
According to the results of the research, 56% of the employees reported they frequently see confidential documents left behind on the printer and a little over half reported that they do not know of any security protocols that are in …
Security Watch – Internet Security News:… – http://www.securitywatch.co.uk/
[ More results from Security Watch – Internet Security News:… ]
Security Information Event Management | CIO – Blogs and Discussion
18 hours ago
Banking, Telecommunications, Power and Energy – anyone and everyone is under internal audit and regulator scrutiny to implement a Security Information Event Management system.
CIO – Blogs and Discussion – – http://advice.cio.com/
[ More results from CIO – Blogs and Discussion – ]
Fergie’s Tech Blog: Cyber Security Czar Front-Runner No Friend of …
8 hours ago by Fergie
Former Republican Congressman Tom Davis, reportedly President Barack Obama’s top candidate for cyber security czar, voted repeatedly to expand the government’s internet wiretapping powers, and helped author the now-troubled national …
Fergie’s Tech Blog – http://fergdawg.blogspot.com/
[ More results from Fergie’s Tech Blog ]
InformationOverload: What is the Biggest Threat to Your …
17 hours ago by ARMA International
The answer is you. A recent study from the Ponemon Institute confirmed previous studies by others that the primary causes of weak information secruity are the organization’s own employees. This study also suggested that employees are …
InformationOverload – http://armablog.typepad.com/informationoverload/
Md. poised to reap cyber security rewards (Baltimore Sun …
4 hours ago by sokdbot
State may win big as increase in federal spending creates jobs, funds research Maryland technology companies that specialize in cyber security are expectin…
Slumped Over Keyboard Dead – http://www.slumpedoverkeyboarddead.com/
[ More results from Slumped Over Keyboard Dead ]
Cyber Security Czar Front-Runner No Friend of Privacy – JustGetThere
9 hours ago by nospam@example.com (JGT)
If picked as cyber security czar, Davis would be given the difficult and sensitive task of coordinating a government-wide strategy to secure the government’s computer networks — as well as help secure the wider internet. That’s a job fraught with perils ranging … But Davis could excel in a new role as cyber security czar, says Marc Rotenberg, who heads the Electronic Privacy Information Center. “He’s a good pick,” Rotenberg says. Read full article. | Share. Comments …
JustGetThere – http://justgetthere.us/blog/ – References
Around The Horn vol.1,125
Apache HTTP DoS tool mitigation, (Sun, Jun 21st)
If you’ve been following our diaries or any other IT Security related news, you probably know about …(more)…
Situational Awareness: Spam Crisis and China, (Sat, Jun 20th)
Gary Warner, Director of Research at the UAB Computer Forensics, posted a very interesting analysis …(more)…
G’day from Sansfire2009, (Sat, Jun 20th)
Well SANSFIRE 2009 is drawing to a close. As you may know SANSFIRE is the SANS conference host …(more)…
Webmedia Explorer Cross Site Scripting Vulnerability
…
phpMyAdmin Code Injection
…
Pantha transLucid Cross Site Scripting and HTML Injection Vulnerabilities
…
Kaspersky PDF Evasion All Products
…
libpurple MSN Protocol SLP Message Heap Overflow Vulnerability
User interaction is not required to exploit this vulnerability.
Related Searches
on Ask.com
Ikarus Multiple Generic Evasions Using CAB ZIP or RAR Files
…
Related Searches
on Ask.com
The Centrality of Red Teaming
By Richard Bejtlich
In my last post I described how a Red Team can improve defense. I wanted to expand on the idea briefly.
First, I believe the modern enterprise is too complex for any individual or group to thoroughly understand how it can be compromised. There are so many links in the chain that even knowing they exist, let alone how they connect, can be impossible.
To flip that on its end, in a complementary way, the modern enterprise is too complex for any individual or group to thoroughly understand how its defenses can fail. The fact that vendors exist to reduce firewall rule sets down to something intelligible by mere mortals is a testament to the apocalyptic fail exhibited by digital defenses.
Furthermore, it is highly likely that hardly anyone cares about attack models until they have been demonstrated. We seen this repeatedly with respect to software vulnerabilities. It can be difficult for someone to take a flaw seriously until a proof of concept is shown to exploit a victim. L0pht’s motto “Making the theoretical practical since 1992” is a perfect summarization of this phenomenon.
So why mention Red Teams? They are central to digital defense because Red Teams transform theoretical intrusion scenarios into reality in a controlled and responsible manner. It is much more realistic to use your incident detection and response teams to know what adversaries are actually doing. However, if you want to be more proactive, you should deploy your Red Team to find and connect those links in the chain that result in a digital disaster.
Richard Bejtlich is teaching new classes in Las Vegas in 2009. Regular Las Vegas registration ends 1 July.
Copyright 2003-2009 Richard Bejtlich and TaoSecurity (taosecurity.blogspot.com and www.taosecurity.com)
Offense and Defense Inform Each Other
By Richard Bejtlich
If you’ve listened to anyone talking about the Top 20 list called the Consensus Audit Guidelines recently, you’ve probably heard the phrase “offense informing defense.” In other words, talk to your Red Team / penetration testers to learn how they can compromise your enterprise in order to better defend yourself from real adversaries.
I think this is a great idea, but there isn’t anything revolutionary about it. It’s really just one step above the previous pervasive mindset for digital security, namely identifying vulnerabilities. In fact, this neatly maps into my Digital Situational Awareness ranking. However, if you spend most of your time writing policy and legal documents, and not really having to deal with intrusions, this idea probably looks like a bolt of lightning!
And speaking of the Consensus Audit Guidelines: hey CAG! It’s the year 2000 and the SANS Top 20 List wants to talk to you!
The SANS/FBI Top Twenty list is valuable because the majority of successful attacks on computer systems via the Internet can be traced to exploitation of security flaws on this list…
In the past, system administrators reported that they had not corrected many of these flaws because they simply did not know which vulnerabilities were most dangerous, and they were too busy to correct them all…
The Top Twenty list is designed to help alleviate that problem by combining the knowledge of dozens of leading security experts from the most security-conscious federal agencies, the leading security software vendors and consulting firms, the top university-based security programs, and CERT/CC and the SANS Institute.
Expect at some point to hear Beltway Bandits talking about how we need to move beyond talking to the Red Team and how we need to see who is actively exploiting us. Guess what — that’s where the detection and response team lives. Perhaps at some point these “thought leaders” will figure out the best way to defend the enterprise is through counterintelligence operations, like the police use against organized crime?
For now, I wanted to depict that while it is indeed important for offense to inform defense, the opposite is just as critical. After all, how is the Red Team supposed to simulate the adversary if it doesn’t know how the adversary operates? A good Red Team can exploit a target using methods known to the Red Team. A great Red Team can exploit a target using methods known to the adversary. Therefore, I created an image describing how offense and defense inform each other. This assumes a sufficiently mature, resourced, and capable set of security teams. 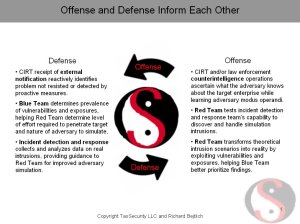
This post may sound sarcastic but I’m not really bitter about the situation. If we keep making progress like this, in 3-5 years the mindset of the information security community will have evolved to where it needed to be ten years ago. I’ll keep my eye on the Beltway Bandits to let you know how things proceed.
Richard Bejtlich is teaching new classes in Las Vegas in 2009. Regular Las Vegas registration ends 1 July.
Copyright 2003-2009 Richard Bejtlich and TaoSecurity (taosecurity.blogspot.com and www.taosecurity.com)
Response to the Möbius Defense
By Richard Bejtlich
One of you asked me to comment on Pete Herzog’s “Möbius Defense”. I like Lego blocks, but I don’t find the presentation to be especially compelling.
- Pete seems to believe that NSA developed “defense in depth” (DiD) as a strategy to defend DoD networks after some sort of catastrophic compromise in the 1970s. DiD as a strategy has existed for thousands of years. DiD was applied to military information well before computers existed, and to the computers of the time before the 1970s as well.
- Pete says DiD is
“all about delaying rather than preventing the advance of an attacker… buying time and causing additional casualties by yielding space… DiD relies on an attacker to lose momentum over time or spread out and thin its massive numbers as it needs to traverse a large area… All the while, various units are positioned to harm the attacker and either cause enough losses in resources to force a retreat or capture individual soldiers as a means of thinning their numbers.”
That’s certainly one way to look at DiD, but it certainly isn’t the only way. Unfortunately, Pete stands up this straw man only to knock it down later. - Pete next says
“Multiple lines of defense are situated to prevent various threats from penetrating by defeating one line of defense. ‘Successive layers of defense will cause an adversary who penetrates or breaks down one barrier to promptly encounter another Defense-In-Depth barrier, and then another, until the attack ends.'”
It would be nice to know who he is quoting, but I determined it is some NSA document because I found other people quoting it. I don’t necessarily agree with this statement, because plenty of attacks succeed. This means I agree with Pete’s criticism here. - So what’s the deal with Möbius? Pete says:
“The modern network looks like a Moebius strip. Interactions with the outside happen at the desktop, the server, the laptop, the disks, the applications, and somewhere out there in the CLOUD. So where is the depth? There is none. A modern network throws all its fight out at once.”
I believe the first section is party correct. The modern enterprise does have many interactions that occur outside of the attack model (if any) imagined by the defenders. The second section is wrong. Although there may be little to no depth in some sections (say my Blackberry) there is plenty of depth elsewhere (at the desktop, if properly defended). The third section is partly correct in the sense that any defense that happens generally occurs at Internet speed, at least as far as exploitation goes. Later phases (detection and response) do not happen all at once. That means time is a huge component of enterprise defense; comprehensive defense doesn’t happen all at once. - Pete then cites “Guerrilla Warfare and Special Forces Operations” as a new defensive alternative to DiD, but then really doesn’t say anything you haven’t heard before. He mentions counterintelligence but that isn’t new either.
I’ve talked about DiD in posts like Mesh vs Chain, Lessons from the Military, and Data Leakage Protection Thoughts.
I think it is good for people to consider different approaches to digital security, but I don’t find this approach to be all that clever.
Richard Bejtlich is teaching new classes in Las Vegas in 2009. Regular Las Vegas registration ends 1 July.
Copyright 2003-2009 Richard Bejtlich and TaoSecurity (taosecurity.blogspot.com and www.taosecurity.com)
Could Opera Unite Be a Botmaster’s Best Friend? (PC World)
In technology
PC World – Opera has added a lot of cool new features to its upcoming Opera 10 browser, and one of them is almost sure to catch the eye of cyber criminals.
Fraudsters Try to Scam Security Expert on EBay
Security expert Bruce Schneier tried to twice sell a used laptop on eBay and each sale was aborted over fraud concerns.
Tech Managers Often Underestimate Impact of Data Loss
Only 7percent of respondents to a survey on data management believed data loss has a “high” impact on a business.
Microsoft’s Free Anti-Malware Debuts Next Week
Microsoft Security Essentials, formerly “Morro,” is scheduled for release next Tuesday for Windows systems.
Women More Security Savvy, Vendor Finds
PC Tools finds men are more often aware of security risks, but few of either gender take the precautions advised.
Twitter Spam Spreads Worm
The malicious zip file contains malware that infects Windows systems but is easily thwarted by antivirus programs.
Could Opera Unite Be a Botmaster’s Best Friend?
Security researchers worry that Opera’s new Unite server feature will be misused by criminals.
Identity Thieves Target Medical Records
Whether stolen data is held for ransom or traded on online black markets, medical identity theft is a growing threat.
Google News Alert for: “cyber security” | cybersecurity | information security | computer security
|
Smart Grid Security Frenzy: Cyber War Games, Worms and Spies, Oh My! |
|
Designated immigration agents authorized to participate in drug … |
|
Somali security minister killed in explosion |
|
Cybersecurity To Push For Standard For Info Security Products |
|
EU Progressing on Information Infrastructure Policy |
|
China Disables Some Google Functions |
|
Will PCI Ever Make the Grade? |
|
Apple: iphone OS 3.0 plugs 46 security bugs |
Google Blogs Alert for: “cyber security” | cybersecurity | information security | computer security
|
Smart Grid Security Frenzy: Cyber War Games, Worms and Spies, Oh My! |
|
Sonos 130 Music System: Review |
|
Social Security Reform – Government Improvement Series |
|
Norway’s government caught spying on itself | IceNews – Daily News |
|
Microsoft Security Essentials Premiering June 23rd ~ Revelations … |
Google News Alert for: “cyber security” | cybersecurity | information security | computer security
|
Public, Private Experts Create Security Guidelines (Opinion) |
|
The next big thing is cybersecurity but what does it mean for us? |
|
A Plan to Secure the Federal Cyberspace |
|
US-Indian security ties boosted after Mumbai: official |
|
Typing In an E-Mail Address, and Giving Up Your Friends’ as Well |
Google Blogs Alert for: “cyber security” | cybersecurity | information security | computer security
|
All Our Might » Blog Archive » PPI panel on cyber security |
|
Computing Research Policy Blog: HOUSE S&T COMMITTEE DISCUSSES … |
|
Free Download Trend Micro Internet Security 3 Months Licence … |
|
Microsoft Security Essentials (MSE or Morro) Rapidshare and Direct … |
|
Spyware: Protect Your Privacy | Nathan’s Plain Tech Talk |
Around The Horn vol.1,124
iPhone OS 3.0 patches 46 known security vulnerabilities
By chris.foresman@arstechnica.com (Chris Foresman) on software
Earlier this week we spoke with security researcher Charlie Miller, who plans to detail a possible method that could allow a hacker to remotely execute arbitrary code on an iPhone. He noted that his method would need to be combined with an exploit of a known vulnerability in the iPhone OS to get the code to execute. The good news for iPhone OS 3.0 users is that Apple has addressed 46 potential security vulnerabilities with the 3.0 update.
The majority of fixes involve the iPhone’s Web-handling capability—WebKit alone got 21 patches while Mobile Safari specifically got two. Several fixes are designed to eliminate cross-site scripting attacks as well as plug memory issues that could potentially lead to arbitrary code execution. Fixes in XML and XLST handling prevent possible disclosure of private information, and a fix in the way JavaScript functions are assigned random IDs helps prevent tracking a user without using cookies. These fixes are especially important as browsers are the most common attack point for most malware.
Click here to read the rest of this article
Acunetix Web Vulnerability Scanner (WVS) 6.5 Released
By Darknet on wvs
You may remember a while back we did a Review of Acunetix Web Vulnerability Scanner 6 – the very full featured web vulnerability scanning software. Well the latest version has been released recently with some updates, bug fixes and improvements on the web application security front. I’m hoping to try out the AcuSensor on a PHP install […]
Relaunched Google Search Service Fingers Malware-Spreading Advertisers
‘Anti-Malvertising’ lets Website owners do background checks on potential online advertisers
Google Expands Site Dedicated to Fighting Malicious Ads
In Search
Google has revamped its Anti-Malvertising site to include more information about fighting malware in online ads. The site also includes a custom search engine that allows users to look up information about advertisers for background checks.
E-Verify extension in contention
The Senate and House would each extend the E-Verify program in their Homeland Security appropriations bills, but they differ on by how long.
New bill seeks to replace Real ID with PASS ID
Legislation that proponents say could revitalize the moribund Real ID program would do so by removing expensive and controversial information technology requirements from current law. However, critics said the new bill would not really solve the problems they see with the program.
Lawmakers differ on DHS data center funding
House and Senate bills to fund the Homeland Security Department in fiscal 2010 are at odds over how much money to give DHS for its data center consolidation program.
DOD’s cyber command takes shape
Defense Department officials are ironing out the details of a new major military command in charge of DOD’s cyber mission. However, they have not made a formal announcement that spells out the new command’s scope.
DHS centralizes cybersecurity programs
Homeland Security Secretary Janet Napolitano said DHS’ many cybersecurity functions have been centralized under Philip Reitinger.
The Biggest Threat? It May Be You
When it comes to virtual server security, you might just be the weak link. Or, more precisely, your lack of planning, maintenance, and governance of that VM server farm.
Database Servers: Candy For Hackers
Sensitive information and poor security administration make tempting targets.
Practical Analysis: Follow The Feds’ Lead In Identity Management
Harnessing the power of a solid identity management system can substantially improve your company’s risk management posture.
Google Tries Blocking Pornography In China
The engineering effort may require disentangling Google.cn from search indexes associated with other Google search sites, like Google.com.
Google Tries Blocking Pornography In China
The engineering effort may require disentangling Google.cn from search indexes associated with other Google search sites, like Google.com.
Google’s Anti-Malvertising.com Fights Off Bad Ads
The site was created because Google has a significant interest in making sure that ad blocking doesn’t become a standard security practice.
Could Opera Unite be a botmaster’s best friend?
Opera has added a lot of cool new features to its upcoming Opera 10 browser, and one of them is almost sure to catch the eye of cyber criminals.
IT managers under-estimate the impact of data loss: survey
A mere seven per cent of respondents to a survey on data management believed data loss has a “high” impact on a business.
Analysis confirms Internet clampdown in Iran
An analysis of the network traffic in and out of Iran over a few days this week during the turmoil surrounding the election is offering a clearer picture of how the manipulation is affecting the ability of its citizens to access certain kinds of online content.
iPhone 3.0 update fixes 46 security flaws
Apple has admitted that the iPhone 3.0 software download patches 46 security holes.
Men are less security savvy than women
When it comes to online security, men are less savvy than women, according to PC Tools.
Tiny-traffic DoS attack spotlights Apache flaw
Denial of Service without the flood
Security guru Robert “RSnake” Hansen has released a novel DoS attack tool that points to a significant flaw in Apache and other webservers.…
US net nanny ratchets Chinese censorware spat
Stall the PC makers. Then sue
US software maker Solid Oak has beefed up efforts to prevent the distribution of China’s “Green Dam” app, continuing to claim that the Far East censorshipware includes code lifted from its own net-filtering tool, Cybersitter.…
Samsung demos OLED security card
Powered by an RFID reader?
Samsung has demoed an electronic ID card with integrated low-power OLED.…
MS names ship date for free security suite
Free as in lunch
Microsoft is launching its free security suite next week – the 23rd of June to be precise.…
Explaining Defense in Depth, (Fri, Jun 19th)
Realizing That You Have a Problem Once an organization reaches a certain size, you end up with a si …(more)…
Cyber Security Review Team to Prepare National Incident Response Plan (June 16 & 17, 2009)
The team that conducted the 60-day review of national cyber security is planning to develop “a comprehensive national incident response plan …….
Jammie Thomas-Rasset Ordered to Pay US $1.92 Million in Music Downloading Case (June 18 & 19, 2009)
On Thursday, a federal jury ruled that Minnesota mother Jammie Thomas-Rasset downloaded music files in “willful violation” of copyright law…….
Experts Suggest Google Cloud Have Security Enabled By Default (June 17, 2009)
Cyber security and privacy experts have written to Google CEO Eric Schmidt, asking that the company “protect users’ communications from theft and snooping by enabling industry standard transport encryption technology (HTTPS) for Google Mail, Docs, and Calendar…….
Stolen Bord Gais Laptop Contains Sensitive Customer Information (June 17 & 18, 2009)
One of four laptop computers stolen from the offices of Irish gas and electricity company Bord Gais contains unencrypted, personally identifiable information of 75,000 Bord Gais customers…….
Company Alleges Chinese Green Dam Filtering Software Contains Stolen Code (June 15, 2009)
A California company is seeking an injunction to bar US companies from shipping PCs loaded with filtering software recently adopted by the Chinese government, alleging that the software contains stolen code…….
Court to Rule in Spanish P2P case (June 15, 2009)
On the heels of the Pirate Bay convictions on charges related to copyright violation, the music industry is anticipating a court ruling later this month in the case of Spanish software designer Pablo Soto…….
Apple Issues iPhone 3.0 (June 18, 2009)
iPhone 3…….
Apple Patches Java Flaws in Mac OS X (June 16, 2009)
Apple has issued updates for Mac OS X and Mac OS X Server to address flaws in its Java virtual machine…….
Botnet Clearinghouse Site Discovered (June 17, 2009)
Researchers say they have uncovered what appears to be a clearinghouse for botnets and malware…….
India to Require Mobile Phones Have IMEI Numbers (June 18, 2009)
The Indian government is now requiring that all imported mobile phones have accompanying International Mobile Equipment Identity (IMEI) numbers; mobile service operators have been ordered to block calls from phones that do not have IMEIs…….
Chinese Government Says Use of Green Dam is Not Mandatory (June 16 & 18, 2009)
A Chinese government official now says that people are not required to use the content filtering software it has mandated be preinstalled on PCs sold in that country as of July 1…….
Researchers to Present Browser-Based Darknet Concept at Black Hat (June 15 & 18, 2009)
Researchers plan to present a proof-of-concept, “zero-footprint” darknet called Veiled at next month’s Black Hat Security Conference…….
Market for Network Firewall Auditing Tools on the Upswing
Forrester Research expects the market for tools to help enterprises manage and audit their firewall policies to jump 25 percent this year due to the requirements of PCI-DSS. Third-party vendors are competing to take advantage of interest in the space by attempting to surpass the capabilities offered by companies like Cisco and Juniper Networks.
– Forrester Research expects the market for firewall auditing tools to jump 25 percent this year on the back of compliance regulations. Right now the market is relatively small, standing at about $30 million today, Forrester analyst John Kindervag said. But the requirements of the Payment Card Indu…
Google Responds to China Internet Porn Crackdown
China has begun blocking Chinese-language search engine results deemed pornographic and is calling on Google to do more to combat explicit content. Google says it has met with government officials there to address the controversy. China’s move follows weeks of controversy over its decision to include Web filtering software with all PCs sold in the country starting next month.
– China has ordered Google to clean up its act when it comes to porn, and has begun blocking some Chinese-language search results, according to a report by China’s official news agency. The move by the government is the latest chapter in its assault on Internet porn, and follows weeks of contro…
Web Fraud 2.0: Franchising Cyber Crime
In Web Fraud 2.0
For the most part, cyber gangs that create malicious software and spread spam operate as shadowy, exclusive organizations that toil in secrecy, usually in Eastern Europe. But with just a few clicks, anyone can jump into business with even the most notorious of these organizations by opening up the equivalent of a franchise operation. Some of the most active of these franchises help distribute malicious software through so-called pay-per-install programs, which pay tiny commissions to the franchise operators, or so-called affiliates, each time a supplied program is installed on an unsuspecting victim’s PC. These installer programs will often hijack the victim’s search results, or steal data from the infected computer. Typically, affiliates will secretly bundle the installers with popular pirated software titles that are made available for download on peer-to-peer file-trading sites. In other cases, the installers are stitched into legitimate, hacked Web sites and quietly foisted upon PCs when
Malicious Attacks Most Blamed in ’09 Data Breaches
In From the Bunker
Rogue employees and hackers were the most commonly cited sources of data breaches reported during the first half of 2009, according to figures released this week by the Identity Theft Resource Center, a San Diego based nonprofit. The ID Theft Center found that of the roughly 250 data breaches publicly reported in the United States between Jan. 1 and Jun. 12, victims blamed the largest share of incidents on theft by employees (18.4 percent) and hacking (18 percent). Taken together, breaches attributed to these two types of malicious attacks have increased about 10 percent over the same period in 2008. Some 44 states and the District of Columbia now have laws requiring entities that experience a breach to publicly disclose that fact. Yet, few breached entities report having done anything to safeguard data in the event that it is lost or stolen. The ITRC found only a single breach in
Brief: Not all apps equal in Iranian filtering
Not all apps equal in Iranian filtering
Brief: Looking back: GhostNet dismantled in a day
Looking back: GhostNet dismantled in a day
Brief: Coming to terms with cyber warfare
Coming to terms with cyber warfare
Free Microsoft Security Software Due Out Next Week (NewsFactor)
In business
NewsFactor – Microsoft’s free software to battle malware will be released Tuesday through its Web site, the company has confirmed. Called Microsoft Security Essentials, it consists of the anti-malware components of Windows Live OneCare, for which there has been an annual charge of $49.95.
How The U.S. Changed Its Security Game (Dr. Dobb’s Journal) (Yahoo News)
Malicious Attacks Most Blamed in ’09 Data Breaches (SecurityFix Blog)
Worm-bearing Twitter spam on the loose (NetworkWorld Virus/Worms)
Google News: “cyber security” | cyber security | information security | computer security
Cybersecurity To Push For Standard For Info Security Products
Bernama – Jun 19, 2009
KUALA LUMPUR, June 19 (Bernama) — CyberSecurity Malaysia, the country’s vanguard of cyber security, is pushing for the Common Criteria for information …
Securing critical infrastructure needs holistic approach, panel says GCN.com
Analysis: One Step Behind Nextgov
Smart Grid Security Frenzy: Cyber War Games, Worms and Spies, Oh My!
Reuters – Katie Fehrenbacher – Jun 18, 2009
According to executives at computer security firm IOActive: Studies show that overall project costs are 60 times higher when gaps in information security …
Smart Meter Security: A Work in Progress
Greentech Media
Itron Highlights Its Continued, Industry-Leading Efforts in … DMN Newswire (press release)
Public, Private Experts Create Security Guidelines (Opinion)
Government Technology – Mark Weatherford – 15 hours ago
Hey, CIOs and chief information security officers (CISOs). Are you looking for an edge to give you more confidence in your cyber-security program? …
Cloud computing: Is it secure enough?
FCW.com
10 Quick Wins for IT Security and FISMA 2009 Compliance GovInfoSecurity.com
Designated immigration agents authorized to participate in drug …
Los Angeles Times – Josh Meyer – Jun 18, 2009
Reporting from Washington — In an effort to plug a hole in US-Mexico drug enforcement, the US departments of Justice and Homeland Security …
DEA makes deal to share drug-bust powers with immigration agents Chicago Tribune
ICE Given More Investigative Power Washington Post
The next big thing is cybersecurity but what does it mean for us?
Examiner.com – 21 hours ago
When President Obama said, “And finally, we will begin a national campaign to promote cyber security awareness and digital literacy from our boardrooms to …
DHS centralizes cybersecurity programs FCW.com
DHS nominee: science for security FederalNewsRadio.com
Free Microsoft Antivirus Software Next Week
New York Times – Riva Richmond – Jun 18, 2009
Contrary to much of the speculation on tech blogs in the last week, Security Essentials will not be an intrusive Web-based service that sucks in information …
How good is Microsoft’s free antivirus software? ZDNet
Microsoft readies free PC security software The Associated Press
A Plan to Secure the Federal Cyberspace
Computerworld – Ariel Silverstone – 21 hours ago
Silverstone also lists his vision for the first (of 23) tasks that he sees as essential for information security in the United States. …
A Plan to Secure the Federal Cyberspace Computerworld
Somali security minister killed in explosion
The Associated Press – Jun 18, 2009
Information Minister Farhan Ali Mohamud announced the death of National Security Minister Omar Hashi Aden but declined to give any other details. …
Somali security minister killed in explosion The Associated Press
US-Indian security ties boosted after Mumbai: official
AFP – 15 hours ago
The US official, when asked to elaborate on the statement, said State Department’s diplomatic security has given India training courses in the past and …
Typing In an E-Mail Address, and Giving Up Your Friends’ as Well
New York Times – Alina Tugend – 14 hours ago
This wasn’t along the lines of someone stealing my bank account information or Social Security number, but I was annoyed and embarrassed. …
Google BlogSearch: “cyber security” | cyber security | information security | computer security
Internet Security Alliance Updates 6-19-09 : Information Security …
20 hours ago by anthonymfreed@gmail.com (Information Security…
The Department of Homeland Security (DHS) Office of Cybersecurity and Communications (CS&C) National Cyber Security Division (NCSD), the Department of Defense (DoD) and National Institute for Standards and Technology (NIST) Information …
Information Security Resources – http://information-security-resources.com/ – References
Offensive Security – Information Security Blog » BackTrack 4 Pre …
18 hours ago by muts
Offensive Security – Information Security Blog. News about Backtrack, Updated Tutorials and VIdeos. BackTrack 4 Pre Final – Public Release and Download. The Remote Exploit Team is ecstatic to announce the public release of BackTrack 4 …
Offensive Security – Information Security Blog – http://www.offensive-security.com/blog/
[ More results from Offensive Security – Information Security Blog ]
IT PRO | Who should be Britain’s cyber security czar?
19 Jun 2009 by IT PRO
Experts reveal what a UK head of cyber security would need to do, while we put forward possible candidates for the role. … worked as CISO and chief security strategist at eBay, chief security officer for Microsoft, and spent some 31 years in US local and federal government with a stint as special advisor for cybersecurity in the White House. According to the ISF, he can draw on experiences across business, government, academic and information security management roles. …
IT PRO – Security – http://www.itpro.co.uk/
Bangalore Information Security Awareness Movement – Blogger News …
18 Jun 2009 by naavi
With a vision to make Bangalore as the “Information Security Capital”, a series of initiatives have been launched in Bangalore one of which is to conduct various programmes on Information Security that would sensitize the society on the …
Blogger News Network – http://www.bloggernews.net/ – References
[ More results from Blogger News Network ]
Information Security in Times of Recession
19 Jun 2009 by iViZ
Recession is a word that sends shivers down the spines of many an industry bigwig. To achieve some serious profits or at the worst to survive the slump, the companies are adopting desperate cost-cutting measures.
3stepADS – Free Advertising Blog – http://www.3stepads.com/
Interview With Chris Potter, PricewaterhouseCoopers Information …
4 hours ago by admin
This entry was posted on Saturday, June 20th, 2009 at 4:04 am and is filed under Computer Security Threat. You can follow any responses to this entry through the RSS 2.0 feed. You can leave a response, or trackback from your own site. …
Jackson Security – http://jacksonsecurity.com/
Shameless Plug #2: 2009 Information Security Summit Pitch Summary …
18 Jun 2009 by Adam Hils
On June 28, 2009, I’ll be delivering my second pitch (along with intrepid colleague, fellow blogger and security raconteur Greg Young for the 2009 Gartner Information Security Summit (session description here). …
Adam Hils – http://blogs.gartner.com/adam-hils/
[ More results from Adam Hils ]
Open Question: I’m a Masters In Information Technology, Student …
14 hours ago by admin
COIS20008 Information Systems Project Planning and Mgment COIS20077 Knowledge Management COIS20078 Data Mining COIS23001 Network Security COIT23002 Computer Graphics COIT23003 Games Development COIT23004 Software Engineering …
Computer Security – http://www.bettercareservices.com/
[ More results from Computer Security ]
Information Security in Times of Recession
19 Jun 2009 by Content Keyword RSS
Information Security in Times of RecessionThe article discusses the move of some companies who are planning a cut in their Information Security spending. It quotes relevant sources to show that in fact, in recession, companies need an …
Learning Forex Trading – http://learning-forex-trading.com/
Despite High Value Of Information, Many Companies Lag On Database …
16 Jun 2009
Despite high value of database information, many companies fail to follow basic database security practices.
DarkReading – All Stories – http://darkreading.com/
Around Then Horn vol.1,123
Microsoft announces free antivirus, limited public beta
By emil.protalinski@arstechnica.com (Emil Protalinski) on Microsoft Security Essentials
Microsoft today officially announced Microsoft Security Essentials (MSE), its free, real-time consumer antimalware solution for fighting viruses, spyware, rootkits, and trojans. Currently being tested by Microsoft employees and a select few testers, MSE is Microsoft’s latest offering intended to help users fight the threats that plague Windows PCs.
Microsoft notes that the threat ecosystem has expanded to include rogue security software, auto-run malware, fake or pirated software and content, as well as banking malware, and the company is aiming to help the users who are not well protected. A beta of MSE will be available in English and Brazilian Portuguese for public download at microsoft.com/security_essentials on June 23, 2009 for the first 75,000 users. This is a target number, but Microsoft is willing to increase it if necessary.
Click here to read the rest of this article
That e-mail attachment is not a Twitter invite
By Elinor Mills
Twitter invites have a URL in the e-mail and not an attachment like this worm attack does, Symantec says.
Symantec is warning about a mass-mailing worm that comes in an attachment pretending to be a Twitter invite.
“The observed messages appear as if they have been sent from …
Microsoft’s free anti-malware beta to arrive next week
By Elinor Mills
Updated at 2:40 p.m. PDT with comment on what happens if a user already has antivirus software installed and at 1:45 p.m. with AVG comment.
Microsoft will launch a public beta of its anti-malware service, Microsoft Security Essentials, on Tuesday as it phases out its Live …
Apple: iPhone OS 3.0 plugs 46 security bugs
By David Martin
Apple has issued an advisory regarding security enhancements included in the iPhone OS 3.0 release Wednesday.
Here is a synopsis of the 46 iPhone security vulnerabilities addressed by the latest operating-system update for the iPhone and iPod Touch. As may be expected, many of these security patches …
Originally posted at iPhone Atlas
Oracle Users Struggle With Patch Management
Oracle users still slow to deploy security patches despite new tools
Microsoft To Launch Free Antivirus Product Next Week
Public beta of the much-anticipated “Morro” tool debuts June 23, replacing OneCare Live for consumers
Hactivist DDoS Attacks In Iran Trigger Worries Of Wider Internet Crackdown
Experts warn that distributed denial-of-service (DDoS) attacks could backfire
New Injection Attack Compromises More Than 40,000 Websites
New injection attack may have compromised more than 40,000 Websites, researchers say
Mass Injectors Still Burying the Needle
In Vulnerability Research
The use of mass injection redirection campaigns like the Gumblar is only just getting started, researchers contend.
Cybersecurity training: The battle over mandates
A debate rages over a Senate proposal to require certification or licensing for all cybersecurity professionals who work on government information systems.
How DOD’s certification program works
DOD published a manual describing various job categories, including technical and management positions, and the different certifications that meet the training requirement. Here are a few examples.
The new cybersecurity licensing proposal
Here’s how a Senate proposal to require certification or even licensing for cybersecurity professionals would work.
Cloud computing: Is it secure enough?
Government officials should start now to understand the security implications and begin taking steps to protect their organizations as they adopt the cloud computing model.
Navy aggressive in protecting networks from enemies
As commander of the Naval Network Warfare Command, Vice Adm. H. Denby Starling leads a 14,000-strong cyber force deployed worldwide to protect Navy information networks.
Deepwater watch: Coast Guard Acquisition Directorate gets new leader
The Coast Guard Acquisition Directorate has a new rear admiral in charge — Ronald Rábago.
Cybersecurity: Legislation, new security controls on same track
New catalog of information and security controls co-developed by NIST, the Pentagon and the intelligence community, along with information security legislation gaining traction in Congress, are expected to significantly improve federal cybersecurity standards.
Google’s Anti-Malvertising.com Fights Off Bad Ads
The site was created because Google has a significant interest in making sure that ad blocking doesn’t become a standard security practice.
Microsoft Security Essentials Beta Coming Tuesday
Previously code-named “Morro,” the free software will replace Windows Live OneCare, which included both security and utility services for $49.95 per year.
Microsoft Security Essentials Beta Coming Tuesday
Previously code-named “Morro,” the free software will replace Windows Live OneCare, which included both security and utility services for $49.95 per year.
Apple iPhone, iPod Security Flaws Get 45 Patches
Software patches were bundled with Apple’s iPhone 3.0 operating system released Wednesday.
iPhone Gets Enterprise IT Boost From Startup Apperian
Apple’s lack of interest in being a major player in enterprise IT has opened the door for Apperian to work with large corporations to develop applications for the iPhone.
MasterCard beefs up security requirements
In a move that is unlikely to sit well with many merchants, MasterCard has quietly changed a key security requirement for all businesses handling between 1 million and 6 million card transactions annually.
Fight against China’s Web filtering software grows
A U.S. company that says its code was copied by a Chinese Internet filtering program has ordered more PC makers not to distribute the Chinese software.
Apple delivers prodigious patch batch for iPhone
Apple on Wednesday patched 46 security vulnerabilities, half of them in the Safari browser and its WebKit rendering engine, for the iPhone and iPod Touch as it released iPhone OS 3.0.
Worm-bearing Twitter spam on the loose
Twitter spam bearing a worm virus is on the loose today trying to lure Twitter users into opening a malicious file attachment containing malware that could take over Windows-based machines, Symantec is warning.
Microsoft to deliver free antimalware next Tuesday
Microsoft will release a public beta of its free antimalware software, now called Microsoft Security Essentials, formerly “Morro,” next Tuesday for Windows XP, Vista and Windows 7.
Spammers cashing in on Twitter, Iran, new iPhone
Spammers are never far from a hot story, it seems, and in the past day they’ve been flooding Twitter with phoney messages about Iran and the latest iPhone 3.0 operating system.
India bans import of mobile phones without identity codes
The Indian government has banned the import of mobile phones without an IMEI (International Mobile Equipment Identity) number, and has ordered operators to block calls from phones without an IMEI from next month..
GhostNet cyber espionage probe still has loose ends
Nearly three months after a report detailed an extensive, worldwide cyber espionage operation, many countries that were hacked may not have been formally notified yet.
Barclays online and ATM crash after disc array fault
A disc array fault left thousands of Barclays customers unable to access their bank accounts online or withdraw money from cash machines in the south of England for three hours yesterday.
EU progressing on information infrastructure policy
The European Union is refining a set of guidelines that would strengthen its ability to respond to computer security crises as well as ensure Internet infrastructure in member countries is more resilient.
Google agrees to delete unblurred German Street View data
Google has agreed to delete some of the original, unblurred photographs captured by its German Street View service, ceding to demands by Hamburg’s Data Protection Office.
Cyberdefense center will lead in education
The Cooperative Cyber Defense Center of Excellence (CCDCOE) opened in May 2008 in Tallinn, Estonia, to assist NATO with technical, legal and policy issues associated with dealing with cyberwarfare incidents. The 20-person center includes civilian analyst Kenneth Geers, who works for the U.S. Navy’s Naval Criminal Investigative Services. Geers, who has been with the center for about a year and a half, spoke about CCDCOE’s mission on the opening day of the organization’s first-ever Conference on Cyber Warfare on Wednesday.
Blogger: Windows 7 UAC feature still vulnerable
The Microsoft blogger who first called attention to a security vulnerability in Windows 7’s User Account Control (UAC) feature claims it still exists and that Microsoft won’t fix it, even as the company nears final code completion on the OS.
Buy an Infected PC for 5 cents
It doesn’t take much to get started in Internet crime these days. Find the right site, hand over $50, and you can start wreaking havoc with 1,000 already-infected PCs.
Canadian bill forces personal data from ISPs sans warrant
Requires police intercept hardware
Canada is considering legislation allowing the country’s police and national security agency to readily access the online communications and the personal information of ISP subscribers.…
January’s Windows 7 hole still open
Sort it out, Redmond
A security hole in Windows 7, highlighted by a blogger back in January, is still wide open and Microsoft is showing very little interest in closing it.…
Incident Handlers Guide to SQL Injection Worms
Category: Incident Handling
Paper Added: June 18, 2009
Building an Automated Behavioral Malware Analysis Environment using Open Source Software
Category: Tools
Paper Added: June 18, 2009
Apache HTTP DoS tool released, (Thu, Jun 18th)
Yesterday an interesting HTTP DoS tool has been released. The tool performs a Denial of Service atta …(more)…
Security researchers develop browser-based darknet
By Robert Westervelt
Called Veiled, the darknet only requires participants to use an HTML 5-based browser to connect and share data anonymously.
Database monitoring, encryption vital in tight economy, Forrester says
By Erin Kelly
A new report from Forrester Research Inc. examines eight database and server data security technologies and recommends small steps that can make a big difference.
Virtual appliances boost flexibility, improve security
By Eric Ogren
Companies see the benefits of placing network-oriented security on a faster processor.
Botnet platform helps cybercriminals bid for zombie PCs
By Robert Westervelt
Infected PCs are sold again and again on a new platform that enables cybercriminals to buy and sell victim’s machines.
FRISK Fprot Generic Bypass Using TAR Files
…
Clam AntiVIrus Generic Bypass Using RAR CAB or ZIP Files
…
CA Service Desk Tomcat Cross Site Scripting Vulnerability
…
Apple Java CColorUIResource Pointer Derference Code Execution Vulnerability
User interaction is required to exploit this vulnerability in that the target must visit a malicious page.
CA ARCserve Backup Message Engine Denial of Service Vulnerabilities
…
Microsoft Preps Security Essentials Beta
Microsoft announces that the beta version of Microsoft Security Essentials, code-named Morro, will be available for download starting June 23. The free product represents Microsoft’s latest swing at the consumer security market, which is dominated by vendors such as Symantec and McAfee.
– Say hello to Microsoft Security Essentials. Microsoft plans to let the newborn brother of its Windows Live OneCare product come out to play next week. Starting June 23, Microsoft will make a beta version of Security Essentials code-named Morro available for download. The offering is slated for…
Why Enterprises Shouldn’t Limit Web Traffic
NEWS ANALYSIS: The business world is deathly afraid of allowing workers to access any site on the Web. A new attack called Nine-Ball, which targets legitimate sites and then redirects users to malicious sites, is just the last security issue that keeps IT administrators up at night. But in the long run, blocking employee access to Websites might be a mistake.
– It’s become commonplace in the business world to limit employee Web traffic. At many firms, regardless of their industry or size, IT managers are being asked to block access to some sites and in some cases, limit the amount of time users spend on the Web. By doing so, they can limit the impact m…
iPhone 3.0 Includes 46 Security Updates
In New Patches
Apple on Wednesday released the much anticipated 3.0 update for the iPhone, bundling at least 46 security fixes into a new version of the iPhone operating system that includes essential functionality such as cut-and-paste and Spotlight search. Included in the 3.0 bundle are security patches for vulnerabilities in a broad range of iPhone components, including Safari and Mail. The mail flaw, for example, could allow a malicious app or attacker to place a phone call without user interaction. A host of other security holes fixed by this update could allow a remote attacker or Web site to run malicious code on the device or cause it to crash. The update is available only through iTunes. My colleague Rob Pegoraro has a more in-depth post about the new features built into this update, but he was having trouble grabbing the update yesterday. Apple says that the automatic update process may take
Microsoft to provide free anti-virus software (AFP)
In technology
AFP – Microsoft has announced it will soon release free anti-virus software so people on tight budgets won’t skimp on protecting their computers from hackers.
Microsoft readies free PC security software (AP)
In technology
AP – Microsoft Corp. said Thursday it plans to release a beta test of its free computer security program next week and is on track to launch a finished product in the fall.
Spammers Cashing in on Twitter, Iran, New IPhone (PC World)
In technology
PC World – Spammers are never far from a hot story, it seems, and in the past day they’ve been flooding Twitter with phoney messages about Iran and the latest iPhone 3.0 operating system.
Microsoft readies free PC security software (AP)
In technology
AP – Microsoft Corp. plans to release a test version of its free computer security program Tuesday.
Microsoft takes on Symantec, McAfee in security (Reuters)
In technology
Reuters – Software giant Microsoft Corp is launching a free PC security service next week in what could be the biggest challenge to date for anti-virus companies with billions of dollars in annual revenue.
Canada proposes new powers to police Internet (AFP)
In technology
AFP – The Canadian government on Thursday unveiled new legislation to allow police to intercept data sent over the Internet and access web subscriber information in order to fight cybercrimes.
EU Progressing on Information Infrastructure Policy (PC World)
In technology
PC World – The European Union is refining a set of guidelines that would strengthen its ability to respond to computer security crises as well as ensure Internet infrastructure in member countries is more resilient.
The Möbius Defense, the end of Defense in Depth
Our new partner in the Netherlands, Lab106 (aka Outpost24), invited me out to present some our research at the Amsterdam Black Hats event.
I focused the main presentation on Anti-Guerrilla Warfare tactics, why defense in depth doesn’t work, and the new Möbius Defense along with…
Google News Alert for: “cyber security” | cybersecurity | information security | computer security
|
Smart Grid Security Frenzy: Cyber War Games, Worms and Spies, Oh My! |
||
|
Designated immigration agents authorized to participate in drug … |
||
|
Somali security minister killed in explosion |
||
|
Cybersecurity To Push For Standard For Info Security Products |
||
|
EU Progressing on Information Infrastructure Policy |
||
|
China Disables Some Google Functions |
||
|
Will PCI Ever Make the Grade? |
||
|
Apple: iphone OS 3.0 plugs 46 security bugs |
Google Blogs Alert for: “cyber security” | cybersecurity | information security | computer security
|
Smart Grid Security Frenzy: Cyber War Games, Worms and Spies, Oh My! |
|
Sonos 130 Music System: Review |
|
Social Security Reform – Government Improvement Series |
|
Norway’s government caught spying on itself | IceNews – Daily News |
|
Microsoft Security Essentials Premiering June 23rd ~ Revelations … |











leave a comment